
Evacuation of 30,000 hackers – Week in security with Tony Anscombe
DEF CON, the annual hacker convention in Las Vegas, was interrupted on Saturday evening when authorities evacuated the event’s venue due to a bomb threat

DEF CON, the annual hacker convention in Las Vegas, was interrupted on Saturday evening when authorities evacuated the event’s venue due to a bomb threat

DEF CON, the annual hacker convention in Las Vegas, was interrupted on Saturday evening when authorities evacuated the event’s venue due to a bomb threat

The limits of current AI need to be tested before we can rely on their output

ESET researchers have observed a new phishing campaign targeting users of the Zimbra Collaboration email server.

When it comes to privacy, it remains complicated and near impossible for a consumer to make an informed decision.

Hiding behind a black box and hoping no one will hack it has been routinely proven to be unwise and less secure.

Search engines, AI, and monetization in the new era

Black Hat is big on AI this year, and for a good reason

Don’t delay: the early access program runs now through December.

Current LLMs are just not mature enough for high-level tasks

Unsurprisingly, artificial intelligence took the center stage at this year’s edition of Black Hat, one of the world’s largest gatherings of cybersecurity professionals

What happens to cyberweapons after a cyberwar?

Listen as ESET’s Director of Threat Research Jean-Ian Boutin unravels the tactics, techniques and procedures of MoustachedBouncer, an APT group taking aim at foreign embassies in Belarus
How ransomware impacts the healthcare industry, including the frequency, root causes of attacks, and data recovery costs.
A social engineering phone call lends authenticity to the attacker’s malicious email

Long-term espionage against diplomats, leveraging email-based C&C protocols, C++ modular backdoors, and adversary-in-the-middle (AitM) attacks… Sounds like the infamous Turla? Think again!

A lighter month than July with just 73 fixes on tap, but a phalanx of advisories and third-party alerts will keep sysadmins bashing away

Sophos earned a 97% “Willingness to Recommend” score and had more customer reviews than the other three Customers’ Choice selections combined.

Naming and shaming the bad guys can be gratifying, but for practical protection, Threat Activity Clusters are the way

A series of ransomware attacks made by different groups share curiously similar characteristics

AI Village talk highlights how generative can be used to automate the creation of fraud campaigns, generating hundreds of fraudulent sites.

Gamers and cybersecurity professionals have something in common – the ever-terrible presence of hacking, scams, and data theft – but how and why would anyone want to target gamers?

When you invest in a company, do you check its cybersecurity? The U.S. Securities and Exchange Commission has adopted new cybersecurity rules.

Browser fingerprinting is supposedly a more privacy-conscious tracking method, replacing personal information with more general data. But is it a valid promise?

With powerful AI, it doesn’t take much to fake a person virtually, and while there are some limitations, voice-cloning can have some dangerous consequences.

“CryptoRom” fake crypto-trading mobile apps pushed through AI-assisted romance scam, using ChatGPT to lure targets.
New insights into how ransomware impacts this sector, including the frequency, root causes of attacks, and data recovery costs.

Current cryptographic security methods watch out – quantum computing is coming for your lunch.

The new SEC cybersecurity rules significantly enhance disclosure requirements, emphasize the board’s role in risk management, and introduce a stringent four-day reporting timeline, necessitating that public companies bolster their cybersecurity strategies, improve incident response processes, and ensure robust communication plans are in place.
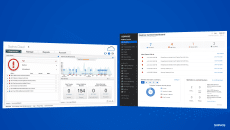
The world’s most trusted cybersecurity platform now secures more than 25 million devices
4909 Murphy Canyon Road Suite, 500
San Diego, CA 92123
Store
Company
Support
Newsletter
Technology Solutions You Can Trust Dismiss