Sophos Announces Plans for New Data Centers in India and Brazil
The new data centers would expand Sophos’ existing base of data centers around the world in the U.S., Canada, Ireland, Germany, Japan, and Australia.
The new data centers would expand Sophos’ existing base of data centers around the world in the U.S., Canada, Ireland, Germany, Japan, and Australia.
No more turning a blind eye to algorithmic bias and discrimination if US lawmakers get their way
The post US: Your AI has to explain its decisions appeared first on WeLiveSecurity

What to know before scanning a QR code – Has your phone been hacked? – Watch your back and keep shoulder surfers at bay
The post Week in security with Tony Anscombe appeared first on WeLiveSecurity

What to know before scanning a QR code – Has your phone been hacked? – Watch your back and keep shoulder surfers at bay
The post Week in security with Tony Anscombe appeared first on WeLiveSecurity
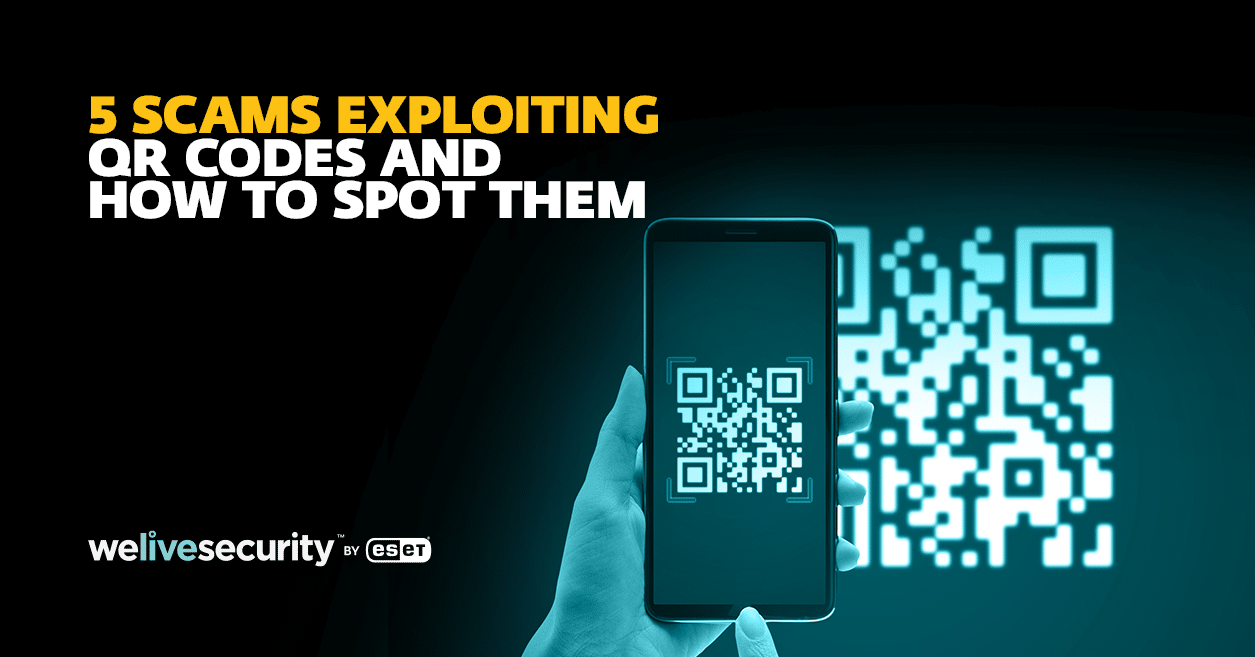
QR codes are all the rage and scammers have taken notice. Look out for dangers lurking behind those little black-and-white squares.
The post Think before you scan: How fraudsters can exploit QR codes to steal money appeared first on WeLiveSecurity

QR codes are all the rage and scammers have taken notice. Look out for dangers lurking behind those little black-and-white squares.
The post Think before you scan: How fraudsters can exploit QR codes to steal money appeared first on WeLiveSecurity

QR codes are all the rage and scammers have taken notice. Look out for dangers lurking behind those little black-and-white squares.
The post Think before you scan: How fraudsters can exploit QR codes to steal money appeared first on WeLiveSecurity
Accelerate threat detection and investigation across your environment.
This latest v19 build adds a number of great new enhancements, including Xstream FastPath Acceleration of IPsec VPN traffic.

Some fraudsters may use low-tech tactics to steal your sensitive information – peering over your shoulder as you enter that data is one of them
The post Shoulder surfing: Watch out for eagle‑eyed snoopers peeking at your phone appeared first on WeLiveSecurity

Some fraudsters may use low-tech tactics to steal your sensitive information – peering over your shoulder as you enter that data is one of them
The post Shoulder surfing: Watch out for eagle‑eyed snoopers peeking at your phone appeared first on WeLiveSecurity

Following an article on January 24, 2022 of Log4Shell scanning and attack detections since the bug was reported, Sophos addresses reader questions about who’s behind it all

Inserting custom file handling rules for a randomly-created file extension and a .LNK in Windows’ startup folder, malware installer created a stealthy persistence mechanism for backdoor.

Zero Trust Network Access boosts remote access security while reducing the network attack surface

At Sophos, we’re committed to helping organizations secure essential resources and we’re proud to be recognized for the continued expansion of our cloud security portfolio. As a global leader in cloud security, we’ve been recognized by CRN®, a brand of The Channel Company, in its annual list of the Coolest Cloud Companies. This list honors
Think your smartphone has been compromised by malware? Here’s how to spot the signs of a hacked phone and how to remove the hacker from your phone.
The post How to tell if your phone has been hacked appeared first on WeLiveSecurity

Kubernetes’ growing status as a fixture of mainstream IT poses a challenge to traditional security approaches.

ESET Research uncovers DazzleSpy malware attacks targeting macOS users – Trading personal data for free online services – PayPal hacking made easy
The post Week in security with Tony Anscombe appeared first on WeLiveSecurity
The trade-off between using a free service and giving up our personal data becomes much less palatable when we think about the wider ramifications of the collection and use of our personal data
The post Beyond the tick box: What to consider before agreeing to a privacy policy appeared first on WeLiveSecurity
Should you beware of wearables? Here’s what you should know about the potential security and privacy risks of your smartwatch or fitness tracker.
The post Every breath you take, every move you make: Do fitness trackers pose privacy risks? appeared first on WeLiveSecurity

Should you beware of wearables? Here’s what you should know about the potential security and privacy risks of your smartwatch or fitness tracker.
The post Every breath you take, every move you make: Do fitness trackers pose privacy risks? appeared first on WeLiveSecurity
Hong Kong pro-democracy radio station website compromised to serve a Safari exploit that installed cyberespionage malware on site visitors’ Macs
The post Watering hole deploys new macOS malware, DazzleSpy, in Asia appeared first on WeLiveSecurity

Somebody could easily take control of your PayPal account and steal money from you if you’re not careful – here’s how to stay safe from a simple but effective attack
The post How I hacked my friend’s PayPal account appeared first on WeLiveSecurity
4909 Murphy Canyon Road Suite, 500
San Diego, CA 92123
Store
Company
Support
Newsletter
Technology Solutions You Can Trust Dismiss