To understand the need for Endpoint Detection and Response (EDR), let’s begin by discussing the cybersecurity environment.
To give a sense of scale, our own cybersecurity experts in SophosLabs process 500,000 never-seen-before malware samples each day. In 2018, the National Institute of Standards and Technology (NIST) reported that 16,451 software vulnerabilities were discovered. The challenge for defenders keeps growing, leading to a desire for better visibility and detection capabilities.
Organizations are having to deal with multiple threats trying to enter their environments on a daily basis. Naturally, many of these threats are stopped outright with strong cybersecurity defenses. But those which are evasive, uncommon, or unclear can slip through, which is where EDR comes into play. EDR was borne out of a need to supplement existing endpoint protection tools.
To make this easier to understand, let’s use a visual example:
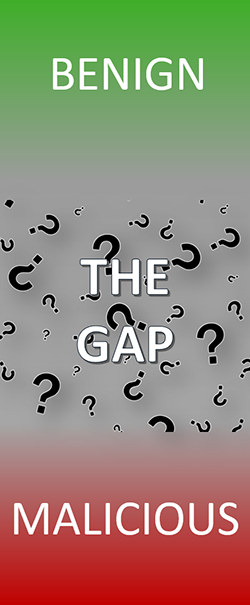
These are non-malicious programs that are part of daily life in the vast majority of organizations, such as Microsoft Word, Outlook or Google Chrome. We don’t want to interfere with them, as this would cause disruption to the wider business.
2. Gray area or ‘the gap’
This area concerns items which aren’t obviously good or bad, so we don’t know whether they are fine to leave or should be blocked without performing further, manual investigation.
EDR was developed to investigate the gap. Are these items actually malicious, requiring action such as isolating affected devices or performing cleanup? Are they Potentially Unwanted Applications (PUAs)? Or something benign that can be ignored?
As threats evolve, many are becoming stealthier, using specific methods to fool antivirus solutions. EDR gives organizations the tools to hunt for suspicious Indicators of Compromise (IOC) and pick up on these hidden threats.
3. Malicious
Malicious files should be stopped outright by strong endpoint and server defenses. These are convicted as malicious and don’t require human interaction. Unfortunately, some traditional EDR tools fail here, letting through malware that should have been caught. This is because their strengths lie with post-event detection rather than pre-emptive protection.
What to look for in an EDR solution
EDR tools can vary wildly in terms of ease of use and granularity of analysis. The key questions to ask when evaluating an EDR solution are:
Read the Top 5 Reasons You Need EDR whitepaper to get more detail on EDR and why it has become a necessity for most organizations. Then take a look at Sophos Intercept X with EDR that combines industry leading protection with powerful, straightforward to use EDR capabilities.
4909 Murphy Canyon Road Suite, 500
San Diego, CA 92123
Store
Company
Support
Newsletter
Technology Solutions You Can Trust Dismiss