
Moving data and other corporate resources to the cloud makes a whole lot of sense, especially with more of us than ever needing flexibility in how, when, and where we get work done.
While cloud providers like AWS give you the flexibility to make your move to the cloud as temporary or permanent as you need, there are some practical considerations you need to manage.
For example, you need to provide users with essential virtual desktop services required for day-to-day work. You also need to provide secure remote access for administrators and developers to private applications running on virtual machines in the cloud, which is the focus of this article.
VPN connections are crucial to enabling secure remote working. Sophos XG Firewall provides two options for creating secure access to services hosted in AWS:
If you have users working remotely the XG Firewall User Portal is a convenient and secure way to access resources within AWS. From it, users can download a customized SSL VPN client software bundle, which includes an SSL VPN client, SSL certificates, and a configuration.
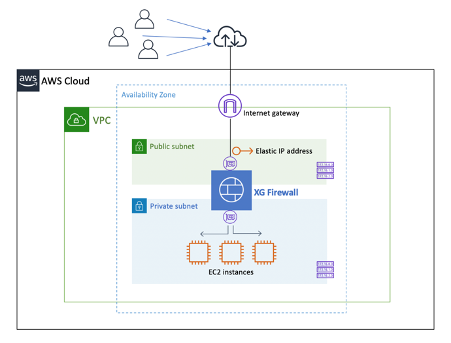
You first need to deploy XG Firewall in your organization’s Virtual Private Cloud (VPC). In the example below, the XG is deployed in a single Availability Zone, with one Elastic Network Interface (ENI) in each of the two subnets, a Public subnet and a Private subnet.
The Public subnet ENI has an Elastic IP address mapped that can be either used directly or in a DNS record. (View instructions for deploying Sophos XG Firewall on AWS).
View SSL VPN Client Instructions or SophosConnect Instructions / Video.
To complete this setup in your AWS console:
If you want the ultimate in VPN reliability and security between your remote workers and your cloud environments, unique to Sophos is the Remote Ethernet Device (RED).
While perhaps not every employee in a business may require a RED, it may be a suitable choice for senior managers and people who deal with confidential information. Using a RED is simple:
Once connected to the router the RED connects back automatically to the XG Firewall (in AWS) and establishes a secure RED Tunnel. (Full Instructions – with video).
Helpful Resources:
4909 Murphy Canyon Road Suite, 500
San Diego, CA 92123
Store
Company
Support
Newsletter
Technology Solutions You Can Trust Dismiss