
The fourth Patch Tuesday of 2021 is another big one. Today, Microsoft revealed 114 vulnerabilities fixed in the monthly security, over half of which could potentially be exploited for remote code execution by attackers. Of the 55 remote execution bugs, over half were tied to Windows’ Remote Procedure Call (RPC) interface. Four more were Microsoft Exchange bugs (all urgent fixes) reported to Micrsoft by the National Security Agency. In addition, six Chrome vulnerabilities that were previously addressed by Google are included in the roll-up.
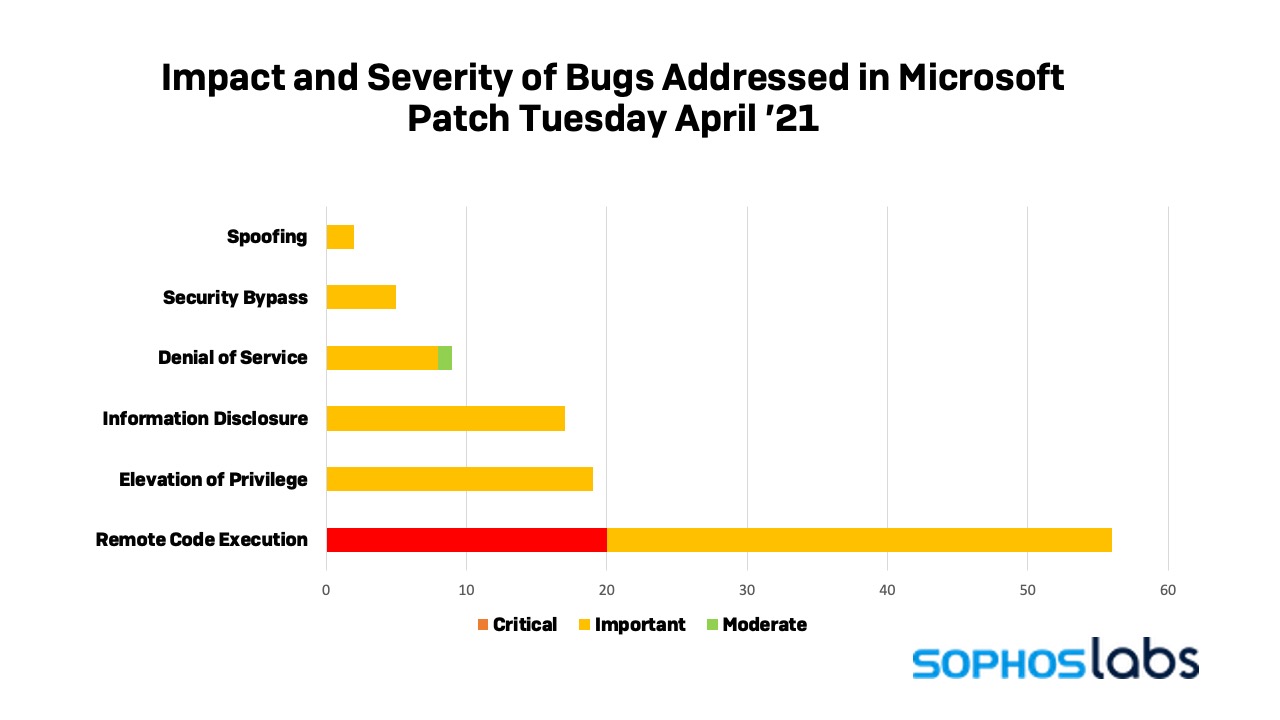
All 20 of the bugs rated as critical to patch by Microsoft in April were remote code execution bugs. A total of 87 were rated as important, and only one was given moderate importance: CVE-2021-28312, a Windows NTFS denial of service vulnerability that is less likely to be exploited.
As with all Patch Tuesdays, Microsoft has published analysis of the major fixes on their Security Updates page. But the release doesn’t ensure that the updates you need will automatically deploy quickly enough to your systems to shut down potential risks. To find and download this month’s Cumulative Update patch yourself, search for the term “2021-04” at the Microsoft Update Catalog website, and select the monthly security rollup that matches your computer’s CPU architecture and build of Windows. You can also read the full technical details about each patch in April’s Security Updates Guide.
A quarter of the vulnerabilities called out this month (28 of them) were in a single Windows component: the Windows RPC interface. Of those, 27 are associated with the RPC runtime itself, and are all potentially exploitable for remote code execution:
The remaining vulnerability, CVE-2021-27091, is an elevation of privileges vulnerability in the RPC Endpoint Mapper Service, rated by Microsoft as important.
Visual Studio Code, Microsoft’s free developer tool, has eight associated remote code execution vulnerabilities patched this month. Five are in Code itself (CVE-2021-28457, CVE-2021-28469, CVE-2021-28473, CVE-2021-28475,and CVE-2021-28477). The remaining three are in extensions—CVE-2021-28470 is a vulnerability in Code’s GitHub Pull Request and Issues extension, CVE-2021-28471 is in Code’s Remote Development Extension, and CVE-2021-28472 is in Code’s Maven for Java extension. There’s also an RCE bug in Visual Studio’s Kubernetes Tools patched in this round (CVE-2021-28448).
Also of note are five remote code execution vulnerabilities patched in Office and its components this month: In the overall Office suite (CVE-2021-28449); in Microsoft Excel (CVE-2021-28451 and CVE-2021-28454); a memory corruption bug in Outlook (CVE-2021-28452) that is remotely exploitable; and in Microsoft Word (CVE-2021-28453). Excel also has an information disclosure vulnerability patched (CVE-2021-28456). And Windows’ Network File System, which has had several bugs over the past few months, has another RCE vulnerability patched in April’s rollup (CVE-2021-28445).
Rounding out the remote code execution vulnerability parade are a number of graphics, image and video related bugs: Windows Media Video Decoder has two critical RCE bugs (CVE-2021-27095 and CVE-2021-28315). Windows’ Raw Image Extension has two RCEs rated by Microsoft as “important” (CVE-2021-28466 and CVE-2021-28468), and there’s; another similarly-rated vulnerability in the VP9 Video Extensions (CVE-2021-28464).
One of the most unusual bugs patched is CVE-2021-27090, an elevation of privilege vulnerability in Windows Secure Kernel Mode. This component is part of Windows’ virtualization-based security (VBS) technology, and has a very small attack surface as it’s strictly isolated by the Hyper-V hypervisor from the rest of the operating system.
Among the more exploitable bugs in April’s fix list are three related to Windows’ TCP/IP driver—two denial of service vulnerabilities (CVE-2021-28319 and 28439) and an information disclosure bug (CVE-2021-28442). CVE-2021-28319 is another bug that harkens back to the “Ping of Death”—the flaw, in the Network Driver Interface Specification driver (ndis.sys), can be triggered remotely by connections using TCP Fast Open option in the TCP/IP protocol. This bug is relatively easy to trigger, and could be exploited to cause a “Blue Screen of Death.”
The information leak bug in TCP/IP (CVE-2021-28442)is also related to TCP Fast Open, but in the TCP driver itself (tcpip.sys). A packet can leverage an overlap in TCP Fast Open and code that provides Local Area Network Denial (LAND) Attack protection in a way that results in tcpip.sys’ TcpSegmentTcbSend() function sending data from uninitialized memory back to the remote system.
Two new elevation of privilege bugs in win32.sys, the kernel driver for Windows’ Graphic Device Interface, are also patched in April. One of them, CVE-2021-28310, is already being exploited in the wild, raising the urgency of the fix.
Here is a list of protection released by SophosLabs in response to this advisory to complement any existing protection and generic exploit mitigation:
| CVE | IPS | SAV |
| CVE-2021-28319 | 2305290 | |
| CVE-2021-28324 | 2305293, 2305294 | |
| CVE-2021-28325 | 2305295, 2305296, 2305299 | |
| CVE-2021-28310 | Exp/2128310-A |
Sophos aims to add detections for critical issues, based on the type and nature of the vulnerabilities, as soon as possible and where we have been given sufficient information to be able to do so. In many cases, existing detections in endpoint products (such as Intercept X) will catch and block exploit attempts without the need for updates.
4909 Murphy Canyon Road Suite, 500
San Diego, CA 92123
Store
Company
Support
Newsletter
Technology Solutions You Can Trust Dismiss