The Sophos X-Ops team, in partnership with the Sophos Firewall product team, is pleased to announce a new application signature pack for Generative AI that has been released for all supported Sophos Firewall versions via a pattern update.
Generative AI has been the subject of considerable buzz recently, and for good reasons. It represents both an enormous opportunity to accelerate or augment workflows as well as a significant threat if abused.
While some organizations have fully embraced Generative AI, many organizations are still exploring the applications for it and evolving their policies for use, and some have outright prohibited it.
Generative AI has proven extremely valuable in several creative and innovative use cases:
Data analysis including trending, benchmarking, modeling, budgeting, and forecasting
Recruitment, on-boarding, training, and employee development
Content summarization and creation for emails, documents, KB articles, social media, and more
Generative AI has also raised legitimate concerns and risks related to trust, data protection, privacy, and intellectual property protection that has many organizations wishing to block access to Generative AI or at least monitor its use.
Sophos has recognized the growing requirements of many organizations to establish Generative AI policies and enforce them. By adding Generative AI app signatures to Sophos Firewall’s in-line CASB and application control capabilities, we are giving organizations full control over which Generative AI solutions they can block, accelerate, or simply monitor.
Sophos Firewall offers important features for easily monitoring and controlling cloud application usage with its in-line Cloud Access Security Broker (CASB) capabilities, which are highlighted on the Sophos Firewall Control Center. This offers a quick, at-a-glance solution to gain visibility into cloud applications – and now Generative AI usage – to identify and control shadow-IT usage and potential data loss vectors.
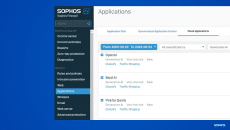
You can easily drill-down to see which specific cloud applications are being accessed on your network that are new, sanctioned, unsanctioned, or tolerated, and build policies to either accelerate, block, or shape this traffic. Generative AI application usage is listed alongside other cloud applications with full traffic volume and user details, providing quick insights and easy classification options:
Insights are also available in both the on-box and Sophos Central reporting as well as the firewall log viewer:
You can use the new Generative AI application signatures to easily add application control rules to enforce your desired policies:
The new Generative AI signature pack is being automatically deployed as a series of pattern updates to all supported Sophos Firewall versions over the next few weeks.
The first signatures are provided in an update Tuesday, August 29th, with new signatures added each week over the following three weeks until all signatures have been deployed by September 19th.
Your firewall device will require either our Web Protection subscription or Xstream Protection bundle (which includes Web Protection) to utilize the application control and CASB cloud application capabilities.
You can check that you have received the new Generative AI signature update by navigating to “Backup & firmware > Pattern updates” and checking that the current version of IPS and Application signatures is version 18.20.86 or later.
To take advantage of the new Generative AI signatures and block, accelerate, and/or route these applications, consult the product documentation:
Sophos Firewall Application Control Documentation and How-to Articles
Sophos Firewall SD-WAN Application Routing
Important note: Prior to this release, OpenAI detection was provided by a signature that was part of the “General Internet” application category. This application signature has now moved to the “Generative AI” category. As a result, any application control policies you previously had related to this application signature may need to be updated.
Also note: The generative AI category and applications are not supported initially in Central Management group policies. This will follow soon.
4909 Murphy Canyon Road Suite, 500
San Diego, CA 92123
Store
Company
Support
Newsletter
Technology Solutions You Can Trust Dismiss