
It’s been a year since the Maze ransomware gang began its rise to notoriety. Previously identified as “ChaCha ransomware” (a name taken from stream cipher used by the malware to encrypt files, the Maze “brand” was first affixed to the ransomware in May of 2019.
Initial samples of Maze were tied to fake websites loaded with exploit kits. Since then, Maze has been delivered by multiple means: exploit kits, spam emails, and—as the group’s operations have become more targeted—Remote Desktop Protocol attacks and other network exploitation.
But aside from the gang’s adjustments in initial compromise approaches, the Maze group has risen in prominence largely because of its extortion tactics: following through on threats of public exposure of victims’ data in public “dumps” of victims’ stolen data, and offering victim data on cybercrime forums if no payment is made.
While Maze did not invent the data-theft/extortion racket, it was among the first ransomware operations to use data theft as a way of twisting the arms of victims to pay up. The Maze gang has made public exposure central to their “brand” identity, and actively seeks attention from press and researchers to promote their brand—and make it easy for victims who might hesitate to pay them to find out their reputation.
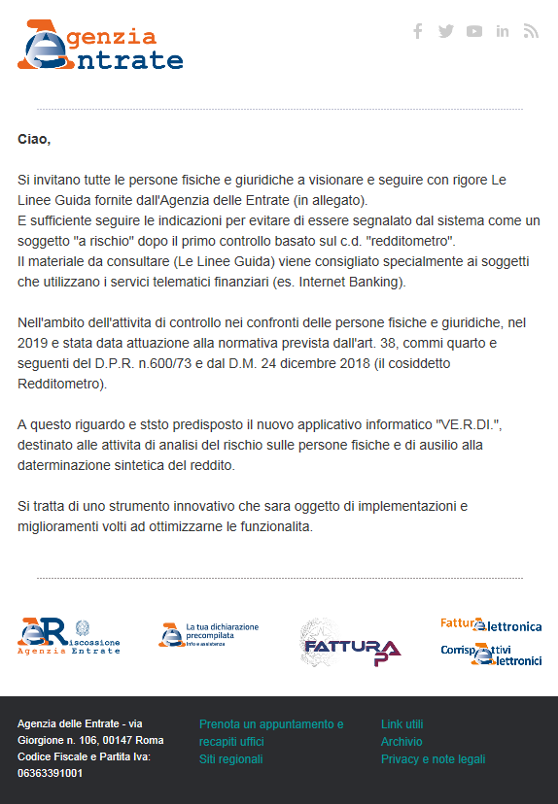
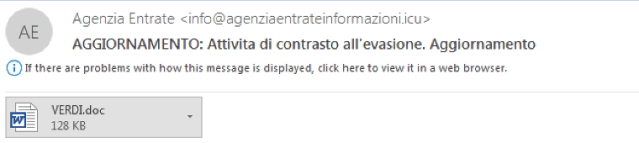
Maze rose to greater attention in October of 2019, when the ransomware’s operators launched a massive spam campaign that masqueraded as messages from government agencies. One campaign sent messages claiming to be from Germany’s Bundeszentralamt fur Steuern (Ministry of Finance), while another posed as a tax message from Italy’s Agencia Entrate (Internal Revenue Service).
The Italian version of the attack claimed to be instructions to avoid being designated as tax cheats, with further details in the attached file VERDI.doc—described as an “interactive tool”, a ploy to trick the user to enable Visual Basic for Applications (VBA) macros. When macros were enabled, the scripts within the document downloaded the Maze ransomware to %TEMP% folder, and then executed it.
Since then, Maze ransomware has gained notice largely from stealing and publishing victims’ data as a means to coerce payment. While threatening to expose victims’ data has long been part of ransomware operators’ playbook, Maze was among the first to follow through on such a threat in a public fashion—starting with the November 2019 exposure of data from Allied Universal.
Maze is not alone in adopting this tactic. REvil/Sodinokibi began releasing data at about the same time as Maze; the DoppelPaymer and Clop ransomware rings have followed suit, and LockBit has added threats of data exposure to its ransom note. But the Maze “team” was the first to go as far as to engage news media to draw attention to its victims, going as far as to include a “press release” on their website.
Maze’s operators seek attention in many ways, in an effort to spread their reputation—and increase the likelihood that their “clients” (as they call their victims) pay quickly. Name recognition is important to them, even as they remain anonymous. One way they seek attention through their provocation of security researchers.
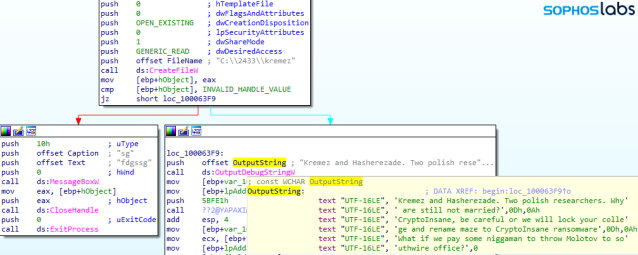
The developers of Maze often drop the names of researchers into strings contained within ransomware binaries or the “packers” that deliver them. For instance, Maze’s authors frequently put researchers’ names in the filenames or file paths for the program database (.pdb) file generated during development.
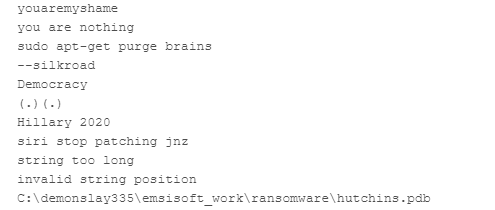
The Maze authors have put names into the .pdb filename and path so frequently that it seems they may be running out of ideas about what to call them:
Sometimes, the Maze authors leave provocative messages to researchers within strings in the code itself. Often these strings have no function, though occasionally they’re used as “kill switches” that shut down the malware’s execution.
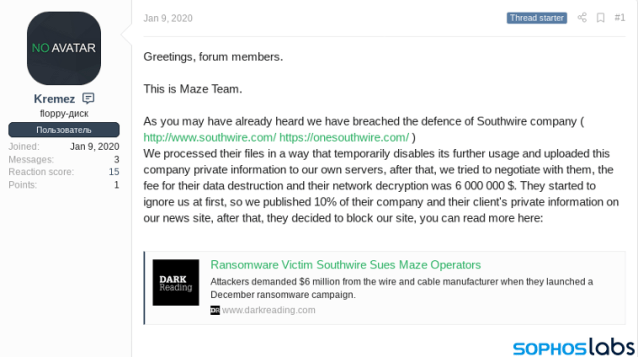
The Maze team’s provocation of researchers extends into its presence in web forums. On one board, the Maze team uses the account name “Kremez”, after prominent ransomware researcher Vitali Kremez, to post links to dumps of data from companies that failed to pay.
But the main platform used to promote the Maze brand is the Maze team’s websites—one specifically for its victims, and another to communicate with the world at large (and encourage victims publicly to pay up).
“Keeping the world safe”
The web panel for victims features the ring’s ironic slogan, “Maze team: Keeping the World safe.”
Victims arriving at the site after following the URL in the ransom note are asked to provide the file DECRYPT-FILES.txt dropped by the ransomware, which contains the identification number assigned to the victim.
Once they’ve identified themselves, victims can upload three files for decryption as proof that the Maze crew can truly restore their data. (Only image files are supported, so no real critical data can be recovered for free.)
The site also provides a chat window, so the victim can communicate with the Maze team’s customer support representatives, who are standing by to answer any questions and negotiate a payment.
Aside from the private web panel provided to victims, the Maze group also maintains a “news” site (hosted both on Tor and on the public Internet) that hosts samples of stolen data for companies that have recently been hit by the ransomware, as well as “full dumps” of data from some companies that failed to negotiate a payment.
The site’s main page is currently a ”press release” dated April 17, 2020. It is really a message to victims, explaining all the bad things that will happen if they ignore Maze’s ransom demand and do not contact them about payment.
They assure “clients” that they honor their side of any agreement and delete stolen data, as their reputation is important to them to conduct business. And they claim to be ready to cut a deal for those hurt by the COVID-19 induced global economic downturn.
In the past, the Maze group has withdrawn data posted to its site due to extenuating circumstances, such as when the group backed off blackmail demands against the City of Pensacola following the shooting of two members of the US Navy at the naval air station there. And in March, the Maze team announced that it would stop attacks on medical organizations until the COVID-19 pandemic “stabilizes.”
In the most recent “press release” (dated April 17, 2020), the operators of Maze wrote:
We are living in the same reality as you are. That’s why we prefer to work under the arrangements and we are ready for compromise. But only with those partners who can understand what is reputation and what are the real consequences of private data loss.
Maze ransomware is mostly written in C++. However, it heavily uses pure assembly with control flow obfuscation This obfuscation includes:
The Maze team is very proud of their main binary’s code obfuscation—in a message in the text of the malware’s binary, they challenged researchers to write an IDAPython script to deobfuscate it. On May 1, Crowdstrike’s Shaun Hurley published a report showing just such a deobfuscation in detail.
Several of the Maze samples we’ve analyzed contain “kill” switches, which when triggered result in the malware not encrypting files. Many of these are there just to grab the attention of researchers, either to send some message or (as mentioned earlier) to name researchers that they know have been examining their code.
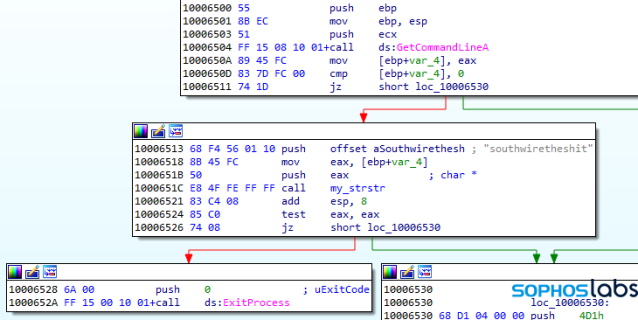
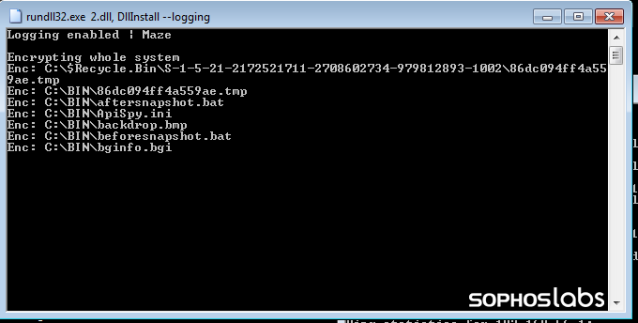
There are also some samples that can be run with more meaningful, functional switches, such as:
Aside from the obfuscation, the Maze main binary’s authors applied a number of anti-analysis techniques to the malware. It checks debugging environment in multiple ways. In addition to using the IsDebuggerPresent API and PEB.BeingDebuggedFlag check , the Maze main binary contains hardcoded hashes of the names for known analysis processes, including procmon.exe, procmon64.exe, x32dbg.exe, x64dbg.exe, ollydbg.exe, procexp.exe, and procexp64.exe. The code enumerates the running processes present, checks processes’ names against the hashed list, and terminates itself if any are detected.
The Maze binary creates persistence by adding itself to Windows’ autorun registry. And it uses a mutex to ensure that another instance of Maze doesn’t execute (unless it’s a sample that has been executed with the –nomutex switch).
As with most ransomware, it deletes shadow copies with the Windows Management Instrumentation command line utility WMIC.exe. The binary also uses the WMI interface to query for antivirus information, executing the Windows Management Instrumentation Query Language (WQL) command “Select * from AntiVirusProduct” within WMI namespace rootSecurityCenter2.
The ransomware collects information about the computer and its user, including information about the system drives, operating system version, default language setting, username, and computer name. As with some other ransomware, Maze will terminate without encrypting files if certain languages are detected (such as those used in Commonwealth of Independent States nations).
Information about the local network its target is connected is also gathered by the malware, by creating a null session connection and enumerating network resources. It tries to find out the role of that the current machine in the network, in order to reuse it in the extortion—Maze varies the amount of the ransom depending on whether the target is a home computer, or a workstation or server on a corporate network.
This information is exfiltrated back to the command and control server using a standard port 80 HTTP POST method, connecting using Windows’ socket library, WS2_32.dll. The URI path is created from a hard-coded string list to building up the URI path.
The malware sends information including the username, drive information, drive free space, language, antivirus product present, and OS version back to the server.
Maze uses RSA and ChaCha20 stream cipher encryption to lock victims’ files. The malware generates an RSA key pair, which is in turn encrypted using the main RSA public key embedded in the malware. As it traverses the file system to encrypt files, it skips the following directories:
Maze also doesn’t encrypt .lnk, .exe, .sys, and .dll files, and specifically avoids the following files:
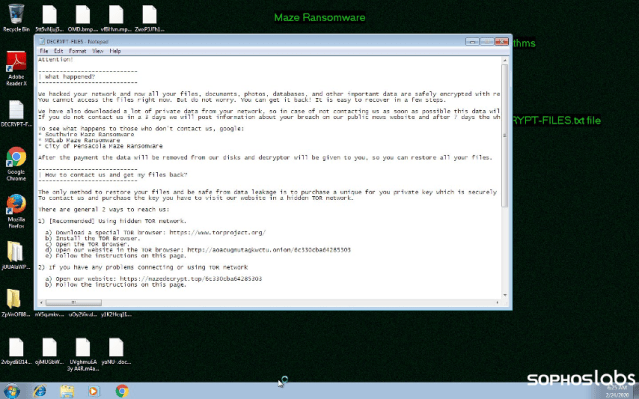
At the end of the encryption, a desktop wallpaper .bmp is dropped—and a voice message is played:
“Alert! *User* Alert! Dear *User*, Your files have been encrypted…”
Both the wallpaper and the voice message are stored in text forms within the binary. The background text is converted to bmp with the use of the DrawTextW and GetDIBits APIs, and is dropped as 000.bmp and set to the wallpaper. The voice message is created using the Microsoft Speech API with the default voice and default audio. Just before playing the message, Before the speech, it uses the operating system’s Beep function to be sure to catch the attention of the victim.
In the latest version of the ransom note, the Maze crew leaves a “friendly” warning for the IT support staff of the victim organization:
| SHA256 | filename |
| 4acba1590552c9b2b82f5a786cedc8a12ca457e355c94f666efef99073827f89 | love.dll |
| 20ea5a9b5b2e47aa191132ac12c1d6dea6b58d7a0467ea53d48e96f8a79c6acd | argfdg, arsgt35yy, maze.exe |
| 3c2be967cbaaafecf8256167ba32d74435c621e566beb06a1ead9d33d7e62d64 | Attack!.rar |
| 7a84d10ac55622cdac25f52170459ae5b8181ee3fc345eb1b1dcbd958b344aa6 | Ave Kim, Emperor.exe |
4909 Murphy Canyon Road Suite, 500
San Diego, CA 92123
Store
Company
Support
Newsletter
Technology Solutions You Can Trust Dismiss