The recent history of Patch Tuesday releases has seen Microsoft updating upwards of 100 software bugs every month, but that trend is broken today when the company fixes just 55 vulnerabilities across their products.
Synchronized to release in parallel with Microsoft’s updates, Adobe is also fixing 11 bugs in their Acrobat Reader software, one of which (CVE-2021-28550/APSB21-29) is reportedly being “exploited in the wild in limited attacks targeting Adobe Reader users on Windows,” according to the company.
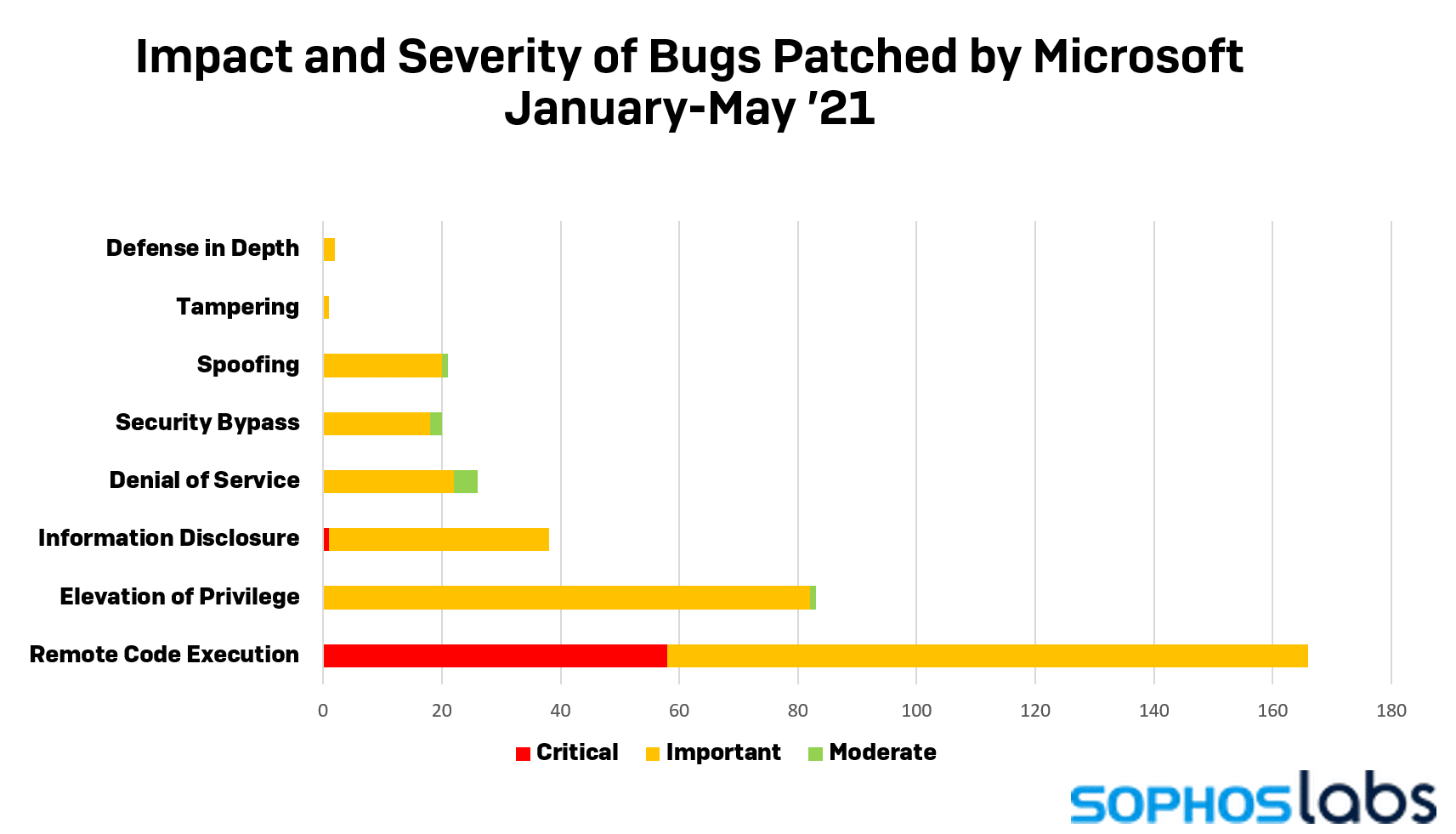
Microsoft did not indicate whether any of the fixes released this month have been exploited in the past, but three of the fixes — in the Windows Scripting Engine, the HTTP Protocol Stack, and the OLE Automation engine — are Critical-rated, remote code execution vulnerabilities. There were 20 total remote code execution bugs stomped out in this release, affecting Office, Sharepoint, the Jet Red database engine, Hyper-V, and various media components, in addition to the previously mentioned critical items.
The updates also include two fixes of “security feature bypass” bugs: One in the client application for Lync (also known as Skype for Business) and one in the SMB Client for Windows. Six privilege escalation bugs were fixed in components relating to Windows Containers, the Docker/Kubernetes implementation on Windows desktops and servers (and related integrations in Visual Studio).
The most oddball, stand out update released this month affects Microsoft’s Wallet service (a now-defunct contactless payment system that was initially shipped in Windows 10 Mobile). The bug, designated CVE-2021-31187, is a privilege escalation vulnerability that affects the 0.03% of the mobile phone market that owns a phone running Windows 10 Mobile.
As with previous Patch Tuesday releases, Microsoft may delay distributing patches to your machine. To find and download this month’s Cumulative Update patch yourself, search for the term “2021-05” at the Microsoft Update Catalog website and select the monthly security rollup that matches your computer’s CPU architecture and build of Windows. You can also read the full technical details about each patch on May’s Security Updates Guide.
We will be updating this post with additional information about the patches throughout the day, after Microsoft publishes technical details.
Here is a list of protection released by SophosLabs in response to this advisory to complement any existing protection and generic exploit mitigation capabilities in our products.
| CVE | IPS | SAV | |
|---|---|---|---|
| XG | EIPS | ||
| CVE-2021-26419 | 2305471 | Exp/2126419-A | |
| CVE-2021-31188 | Exp/2131188-A | ||
| CVE-2021-31181 | 2305473,2305472 | 2305473,2305472 | |
| CVE-2021-31166 | 2305495 | 2305495 | |
4909 Murphy Canyon Road Suite, 500
San Diego, CA 92123
Store
Company
Support
Newsletter
Technology Solutions You Can Trust Dismiss