
Fake friends and followers on social media – and how to spot them
One of the biggest threats to watch out for on social media is fraud perpetrated by people who aren’t who they claim to be. Here’s how to recognize them.

One of the biggest threats to watch out for on social media is fraud perpetrated by people who aren’t who they claim to be. Here’s how to recognize them.

One of the biggest threats to watch out for on social media is fraud perpetrated by people who aren’t who they claim to be. Here’s how to recognize them.

One of the biggest threats to watch out for on social media is fraud perpetrated by people who aren’t who they claim to be. Here’s how to recognize them.

One of the biggest threats to watch out for on social media is fraud perpetrated by people who aren’t who they claim to be. Here’s how to recognize them.

ESET researchers discovered a cyberespionage campaign against a governmental entity in Guyana

ESET researchers discovered a cyberespionage campaign against a governmental entity in Guyana

ESET researchers discovered a cyberespionage campaign against a governmental entity in Guyana

ESET researchers discovered a cyberespionage campaign against a governmental entity in Guyana

ESET researchers discovered a cyberespionage campaign against a governmental entity in Guyana

ESET researchers discovered a cyberespionage campaign against a governmental entity in Guyana

ESET researchers discovered a cyberespionage campaign against a governmental entity in Guyana

ESET researchers discovered a cyberespionage campaign against a governmental entity in Guyana

ESET researchers discovered a cyberespionage campaign against a governmental entity in Guyana

Start taking advantage of all the great new features in SFOS v20 today.

Start taking advantage of all the great new features in SFOS v20 today.
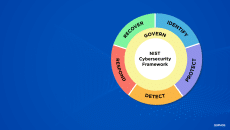
Sophos can help organizations in their efforts to align with the NIST CSF and other cybersecurity frameworks.

Start taking advantage of all the great new features in SFOS v20 today.

Four key actions to help improve your cyber safety

In an increasingly complex and interconnected digital landscape, personal cybersecurity empowers you to protect your data, privacy and digital well-being

In an increasingly complex and interconnected digital landscape, personal cybersecurity empowers you to protect your data, privacy and digital well-being

In an increasingly complex and interconnected digital landscape, personal cybersecurity empowers you to protect your data, privacy and digital well-being

In an increasingly complex and interconnected digital landscape, personal cybersecurity empowers you to protect your data, privacy and digital well-being

In an increasingly complex and interconnected digital landscape, personal cybersecurity empowers you to protect your data, privacy and digital well-being

In an increasingly complex and interconnected digital landscape, personal cybersecurity empowers you to protect your data, privacy and digital well-being

In an increasingly complex and interconnected digital landscape, personal cybersecurity empowers you to protect your data, privacy and digital well-being

In an increasingly complex and interconnected digital landscape, personal cybersecurity empowers you to protect your data, privacy and digital well-being

In an increasingly complex and interconnected digital landscape, personal cybersecurity empowers you to protect your data, privacy and digital well-being

During the attack, the group deployed several tools, most notably a newly-discovered sophisticated backdoor that ESET named LightlessCan

During the attack, the group deployed several tools, most notably a newly-discovered sophisticated backdoor that ESET named LightlessCan

During the attack, the group deployed several tools, most notably a newly-discovered sophisticated backdoor that ESET named LightlessCan
4909 Murphy Canyon Road Suite, 500
San Diego, CA 92123
Store
Company
Support
Newsletter
Technology Solutions You Can Trust Dismiss